Juniper Networks SSG 320M and 350M Security Policy
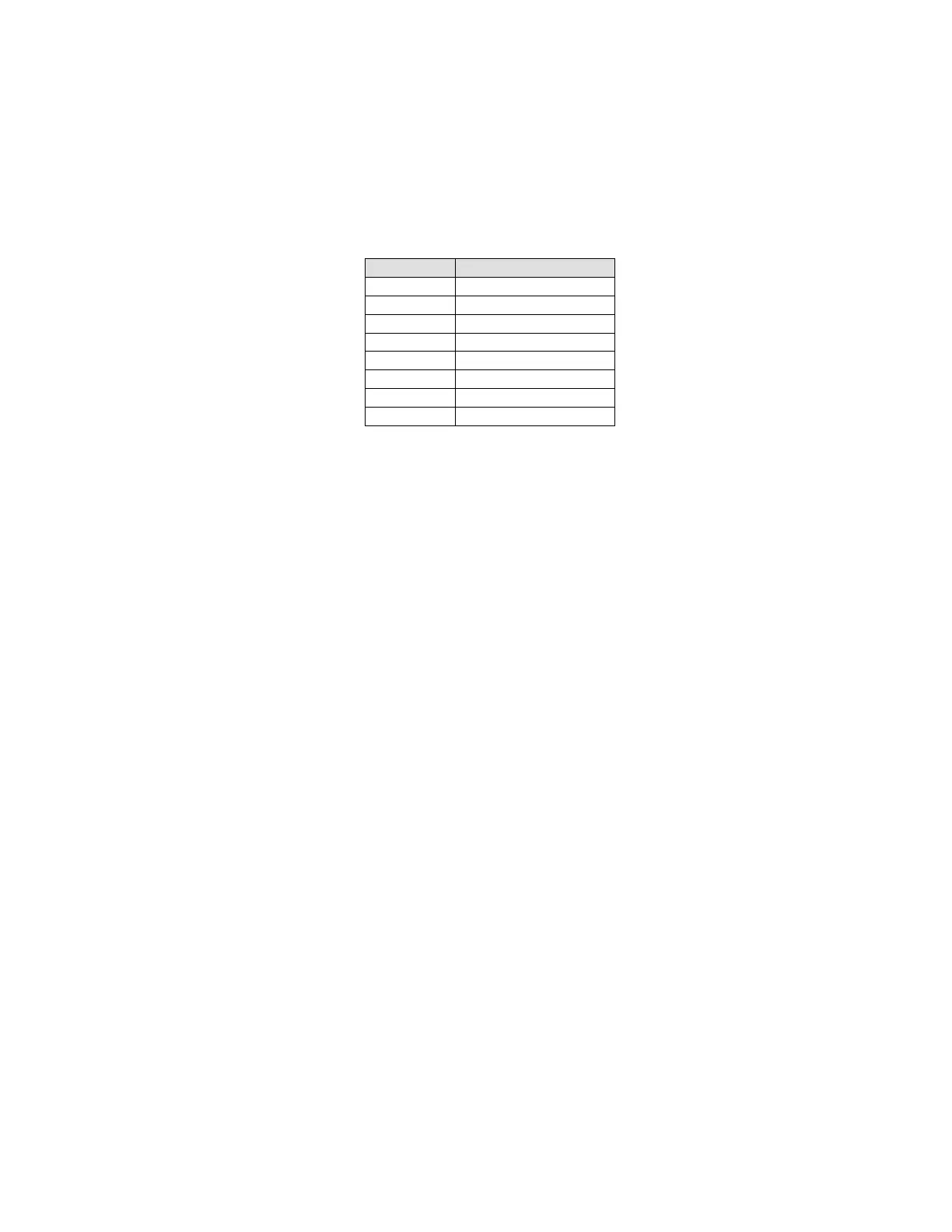
Cryptographic Algorithm Validation
Cryptographic algorithm validation certificate numbers for are listed in the table below:
Table 7: Algorithm Validation Certificates
Critical Security Parameter (CSP) Definitions
Below is a list of Critical Security Parameter (CSP) definitions:
IPSEC HMAC SHA-1 Key: Used by IPsec for data integrity.
IPSEC ESP Key: Triple-DES, and AES for user traffic encryption.
IKE Pre-Shared Key: Used during the IKE protocol to establish cryptographic keys to be
used by IKE.
IKE Encryption Key: Triple-DES, and AES for peer-to-peer IKE message encryption.
IKE HMAC SHA-1 Key: Used by IKE for data integrity.
Password: Crypto-Officer and User passwords.
SSH Server/Host DSA Private Key: Used to create digital signatures.
SSH Encryption Key: Triple-DES encryption key to encrypt telnet commands.
SSH HMAC SHA-1 Key: Used by SSH for data integrity.
HA Key: AES Encryption key for HA data.
IKE RSA/DSA/ECDSA Private Key: RSA/DSA/ECDSA key used in IKE identity
authentication.
Diffie Hellman Private Key Components: Used during the DH key agreement protocol.
PRNG Seed and Seed Key: Used during the ANSI X9.31 generation of pseudo random
numbers.
RADIUS Secret Key: Used to authenticate exchanges with the RADIUS server
Public Key Definitions
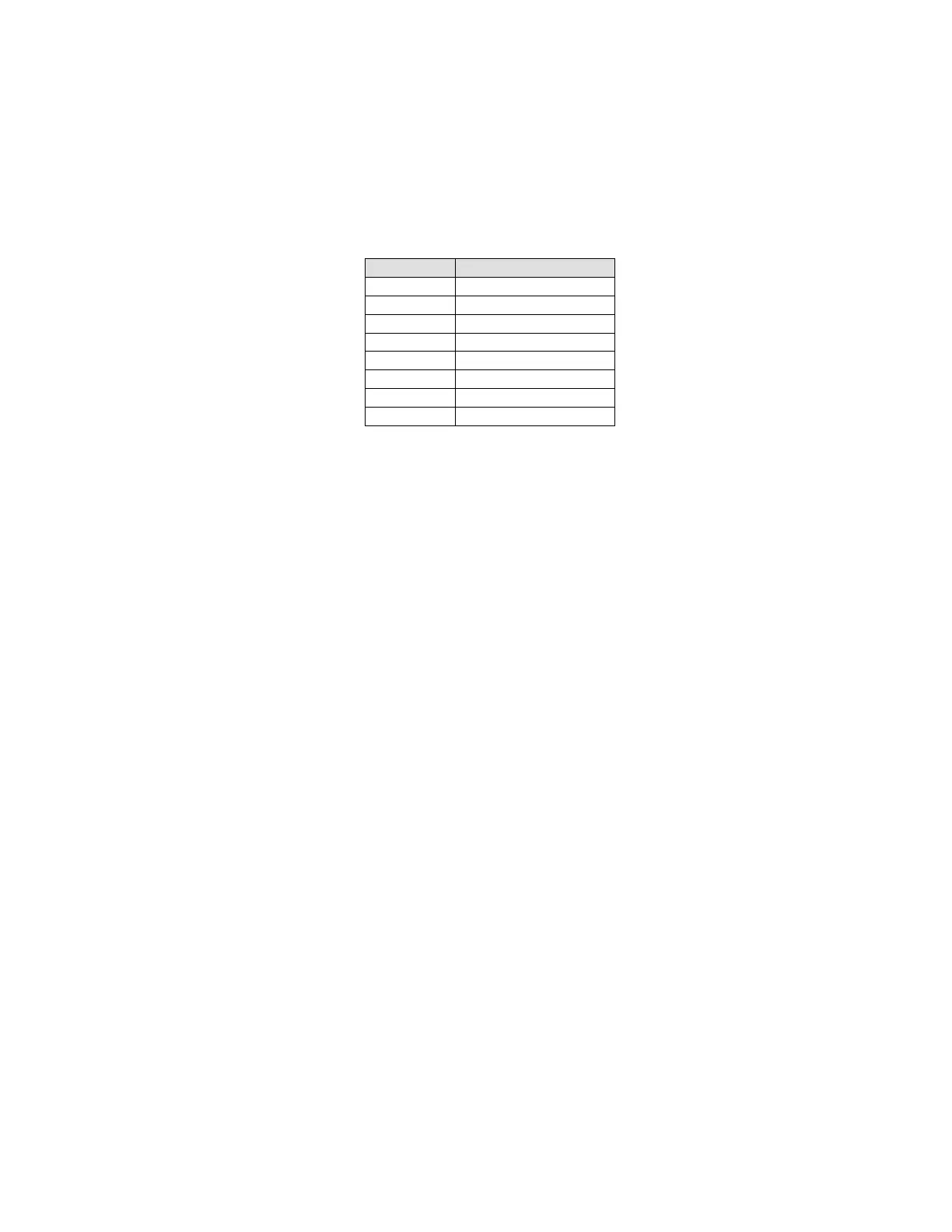 Loading...
Loading...