6-13
Configuring Secure Shell (SSH)
Configuring the Switch for SSH Operation
3. Provide the Switch’s Public Key to Clients
When an SSH client contacts the switch for the first time, the client will
challenge the connection unless you have already copied the key into the
client’s "known host" file. Copying the switch’s key in this way reduces the
chance that an unauthorized device can pose as the switch to learn your access
passwords. The most secure way to acquire the switch’s public key for
distribution to clients is to use a direct, serial connection between the switch
and a management device (laptop, PC, or UNIX workstation), as described
below.
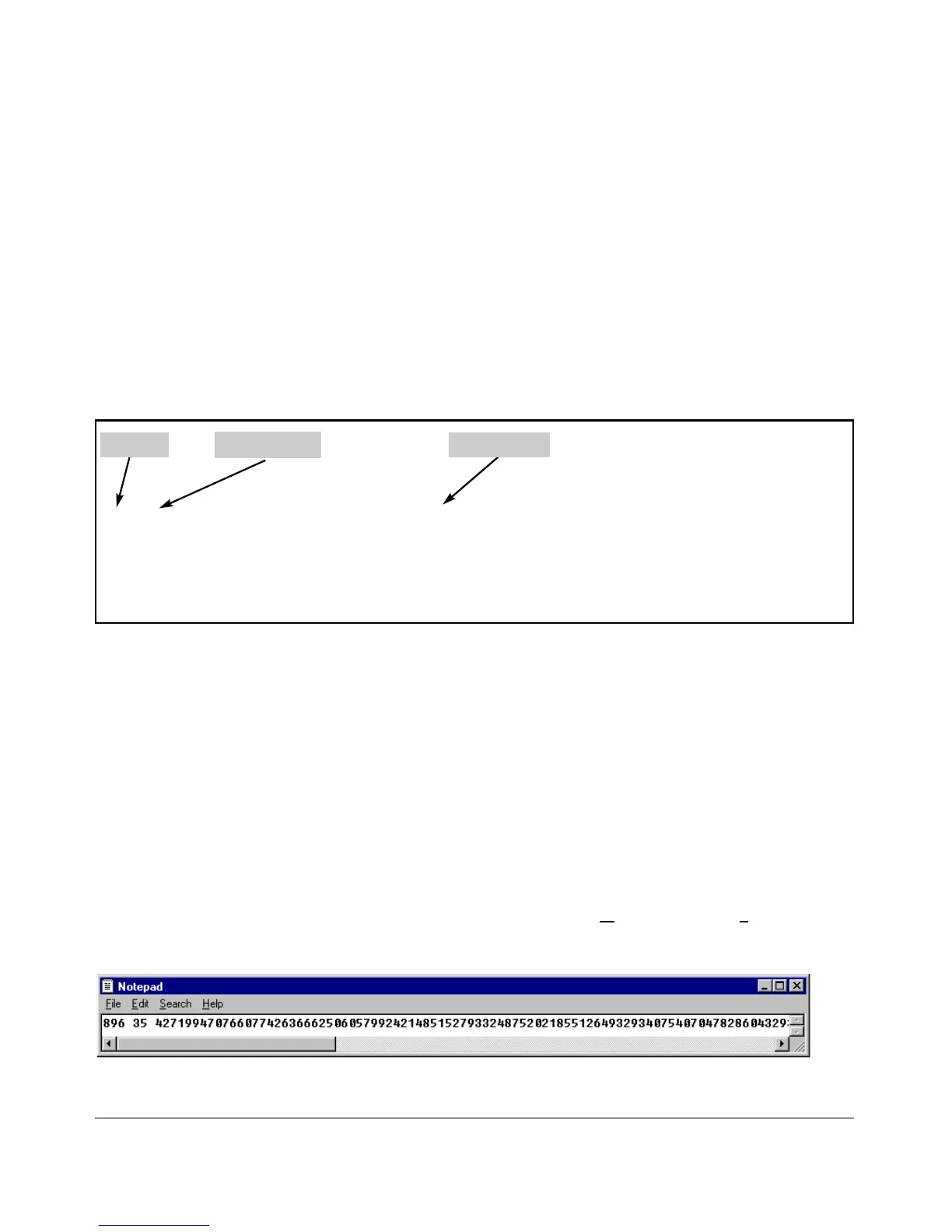
The public key generated by the switch consists of three parts, separated by
one blank space each:
Figure 6-6. Example of a Public Key Generated by the Switch
(The generated public key on the switch is always 896 bits.)
With a direct serial connection from a management station to the switch:
1. Use a terminal application such as HyperTerminal to display the switch’s
public key with the show crypto host-public-key command (figure 6-5).
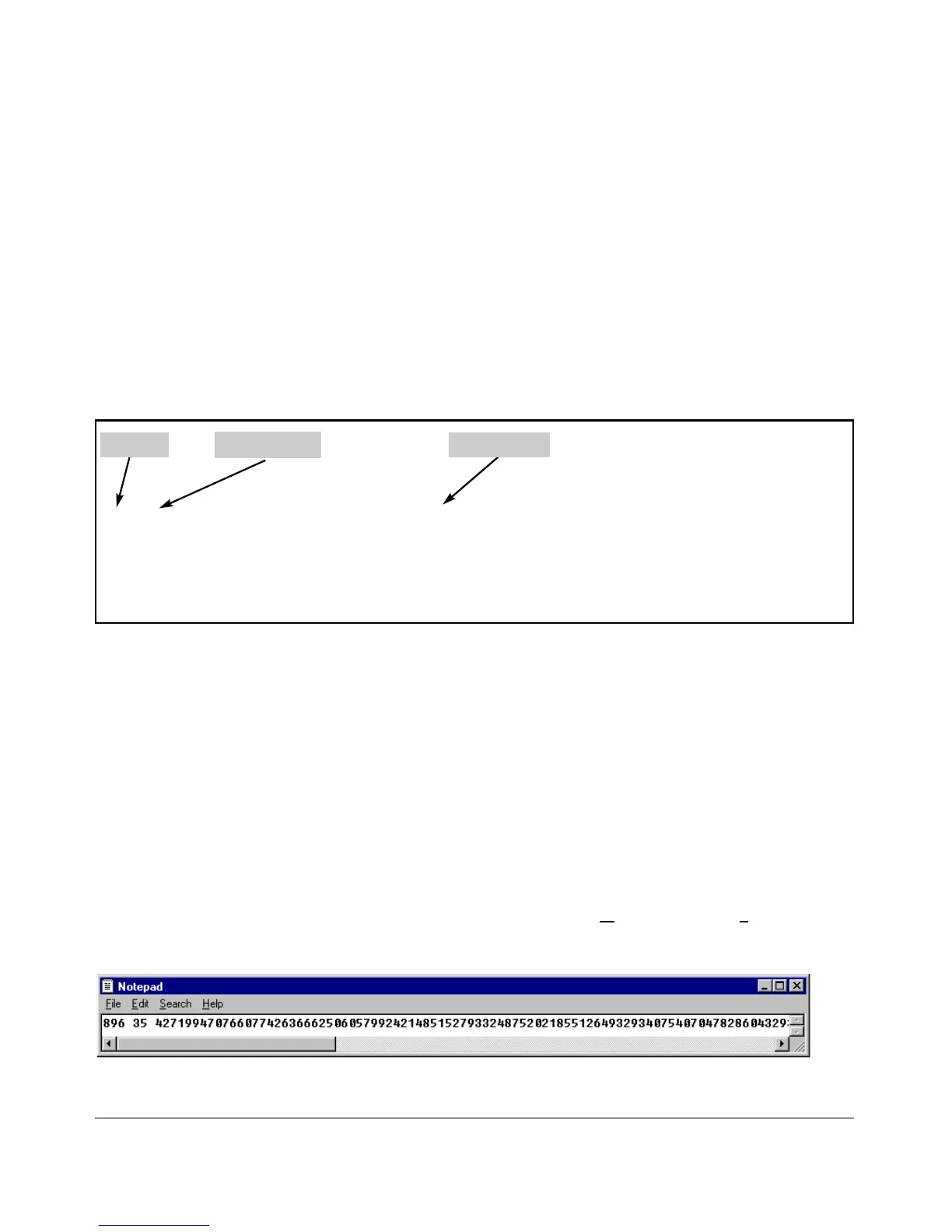
2. Bring up the SSH client’s "known host" file in a text editor such as Notepad
as straight ASCII text, and copy the switch’s public key into the file.
3. Ensure that there are no changes in breaks in the text string. (A public
key must be an unbroken ASCII string. Line breaks are not allowed
Changes in the line breaks will corrupt the Key.) For example, if you are
using Windows® Notepad, ensure that W
ord Wrap (in the Edit menu) is
disabled, and that the key text appears on a single line.
Figure 6-7. Example of a Correctly Formatted Public Key

 Loading...
Loading...