9-22
Configuring and Monitoring Port Security
MAC Lockdown
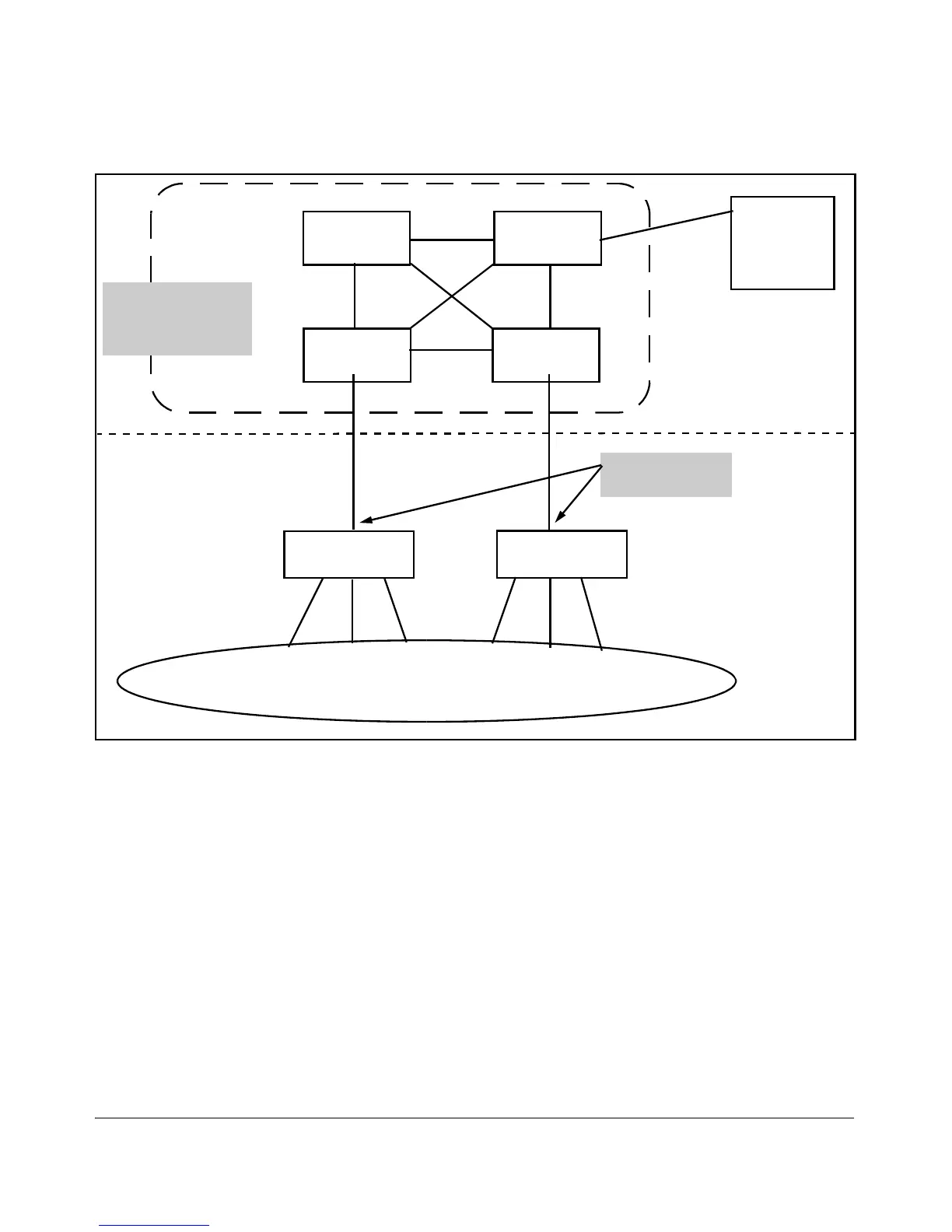
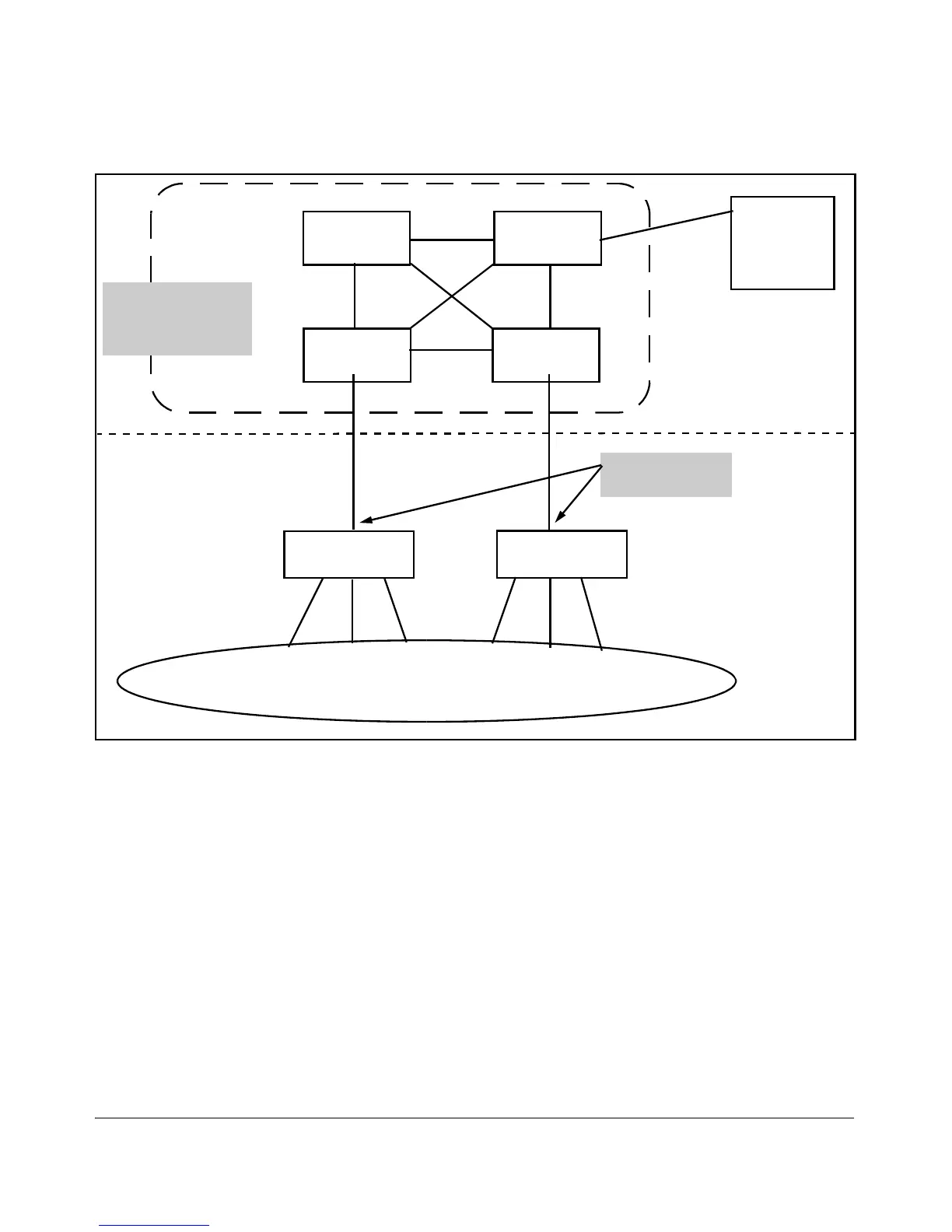
Figure 9-9. MAC Lockdown Deployed At the Network Edge Provides Security
Basic MAC Lockdown Deployment. In the Model Network Topology shown
above, the switches that are connected to the edge of the network each have
one and only one connection to the core network. This means each switch has
only one path by which data can travel to Server A. You can use MAC
Lockdown to specify that all traffic intended for Server A’s MAC Address must
go through the one port on the edge switches. That way, users on the edge can
still use other network resources, but they cannot “spoof” Server A and hijack
data traffic which is intended for that server alone.
 Loading...
Loading...