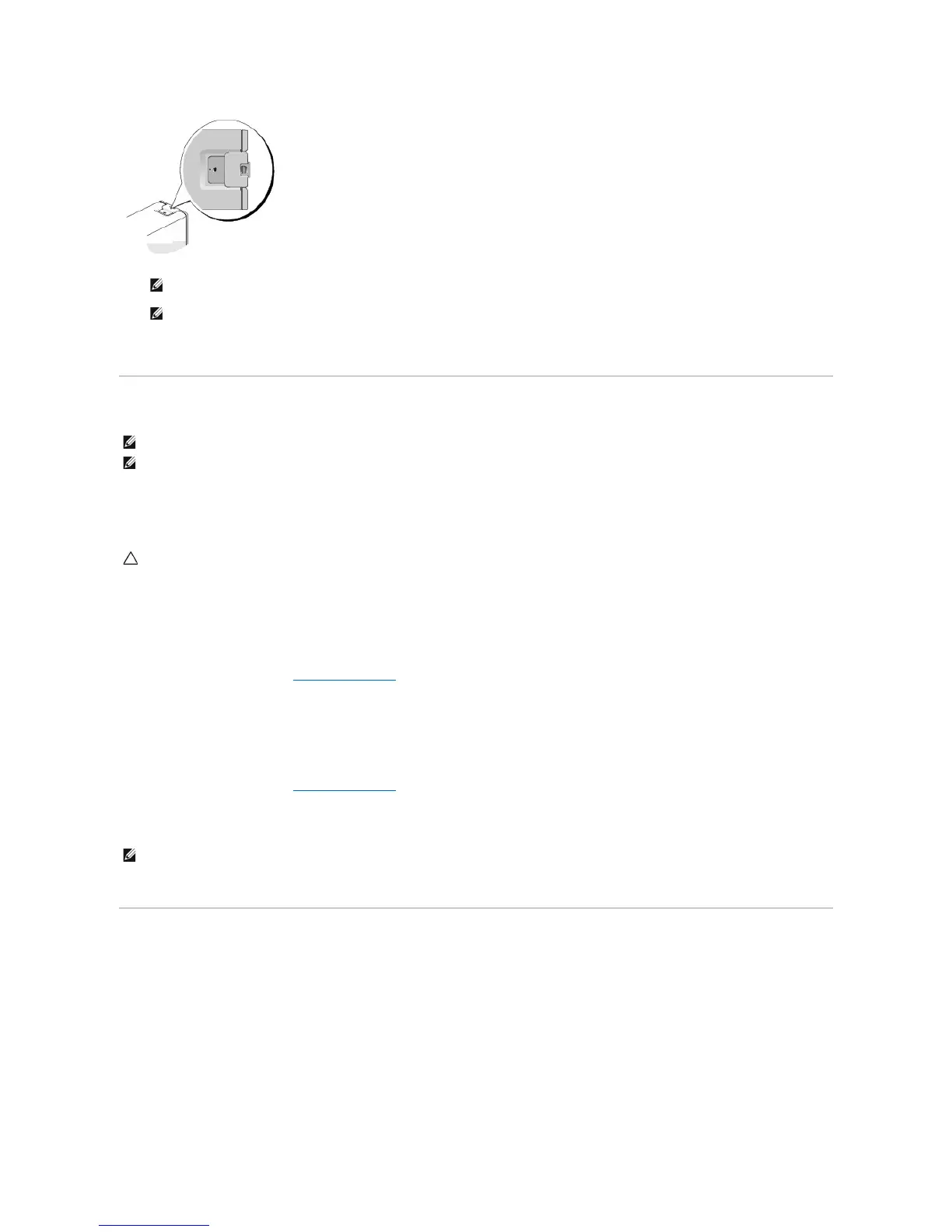
Antitheft devices usually include a segment of metal-stranded cable with an attached locking device and key. The documentation that comes with the
device contains instructions for installing it.
Trusted Platform Module (TPM)
TPM is a hardware-based security feature that can be used to create and manage computer-generated encryption keys. When combined with security
software, the TPM enhances existing network and computer security by enabling features such as file protection capabilities and protected e-mail. The TPM
feature is enabled through a system setup option.
Enabling the TPM Feature
1. Enable the TPM software:
a. Enter System Setup (see Entering System Setup).
b. Select Security® TPM Security and press <Enter>.
c. Under TPM Security, select On.
d. Save and exit the system setup program.
2. Activate the TPM setup program:
a. Enter System Setup (see Entering System Setup).
b. Select Security® TPM Activation and press <Enter>.
c. Under TPM Activation, select Activate and press <Enter>.
d. Once the process is complete, the computer either restarts automatically or prompts you to restart your computer.
Security Management Software
The security management software is designed to utilize four different features to help you secure your computer:
l Log-in management
l Pre-boot authentication (using a fingerprint reader, smart card, or password)
l Encryption
l Private information management
For information about how to use the software and the different security features, see Getting Started Guide for the software:
Click Start® All Programs® Wave Systems Corp® Getting Started Guide.
CAUTION: To secure your TPM data and encryption keys, follow the backup procedures documented in the Archive and Restore section of the
EMBASSY Security Center help file. In the event of these backups being incomplete, lost, or damaged, Dell will be unable to assist in the recovery
of encrypted data.
 Loading...
Loading...