10-7
Catalyst 3750 Switch Software Configuration Guide
OL-8550-02
Chapter 10 Configuring IEEE 802.1x Port-Based Authentication
Understanding IEEE 802.1x Port-Based Authentication
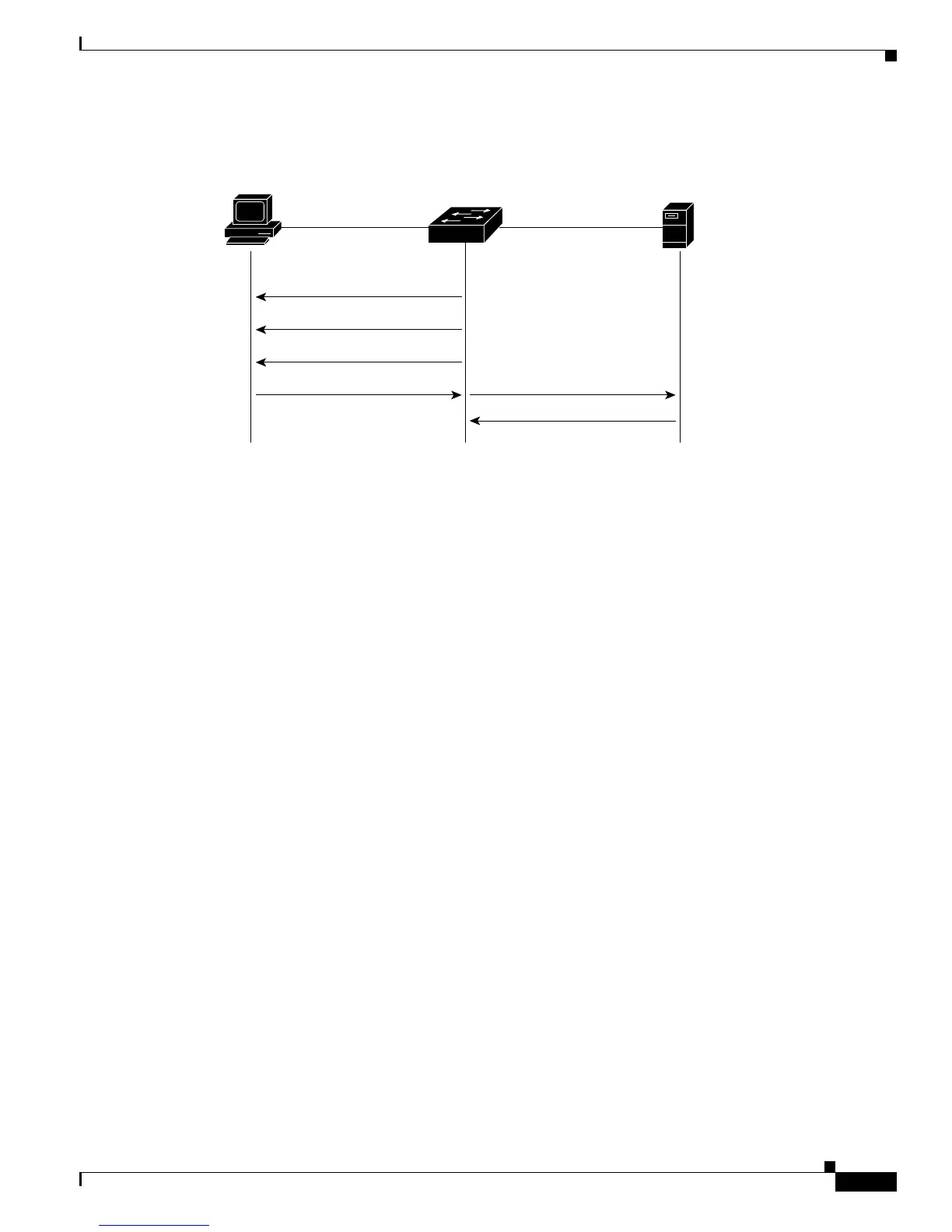
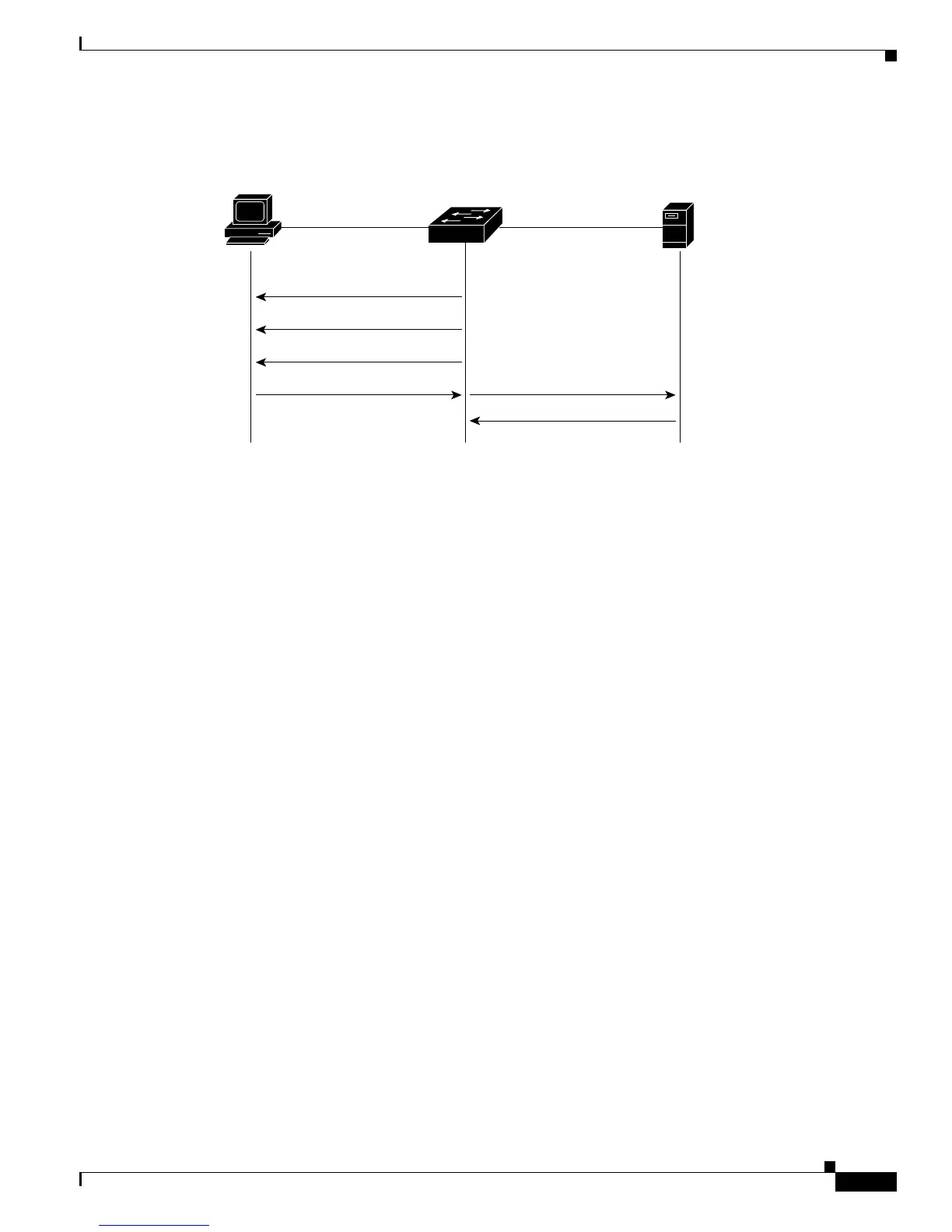
Figure 10-4 Message Exchange During MAC Authentication Bypass
Ports in Authorized and Unauthorized States
During IEEE 802.1x authentication, depending on the switch port state, the switch can grant a client
access to the network. The port starts in the unauthorized state. While in this state, the port that is not
configured as a voice VLAN port disallows all ingress and egress traffic except for IEEE 802.1x
authentication, CDP, and STP packets. When a client is successfully authenticated, the port changes to
the authorized state, allowing all traffic for the client to flow normally. If the port is configured as a voice
VLAN port, the port allows VoIP traffic and IEEE 802.1x protocol packets before the client is
successfully authenticated.
If a client that does not support IEEE 802.1x authentication connects to an unauthorized IEEE 802.1x
port, the switch requests the client’s identity. In this situation, the client does not respond to the request,
the port remains in the unauthorized state, and the client is not granted access to the network.
In contrast, when an IEEE 802.1x-enabled client connects to a port that is not running the IEEE 802.1x
standard, the client initiates the authentication process by sending the EAPOL-start frame. When no
response is received, the client sends the request for a fixed number of times. Because no response is
received, the client begins sending frames as if the port is in the authorized state.
You control the port authorization state by using the dot1x port-control interface configuration
command and these keywords:
• force-authorized—disables IEEE 802.1x authentication and causes the port to change to the
authorized state without any authentication exchange required. The port sends and receives normal
traffic without IEEE 802.1x-based authentication of the client. This is the default setting.
• force-unauthorized—causes the port to remain in the unauthorized state, ignoring all attempts by
the client to authenticate. The switch cannot provide authentication services to the client through the
port.
• auto—enables IEEE 802.1x authentication and causes the port to begin in the unauthorized state,
allowing only EAPOL frames to be sent and received through the port. The authentication process
begins when the link state of the port changes from down to up or when an EAPOL-start frame is
received. The switch requests the identity of the client and begins relaying authentication messages
between the client and the authentication server. Each client attempting to access the network is
uniquely identified by the switch by using the client MAC address.
141681
Client
Switch
EAPOL Request/Identity
EAPOL Request/Identity
EAPOL Request/Identity
RADIUS Access/Request
RADIUS Access/Accept
Ethernet packet
Authentication
server
(RADIUS)

 Loading...
Loading...