3.1.1 CIP 002
CIP 002 concerns itself with the identification of:
● Critical assets, such as ov
erhead lines and transformer
s
● Critical cyber assets, such as IEDs that use routable protocols to communicate outside or inside the
Electronic Security Perimeter; or are accessible by dial-up
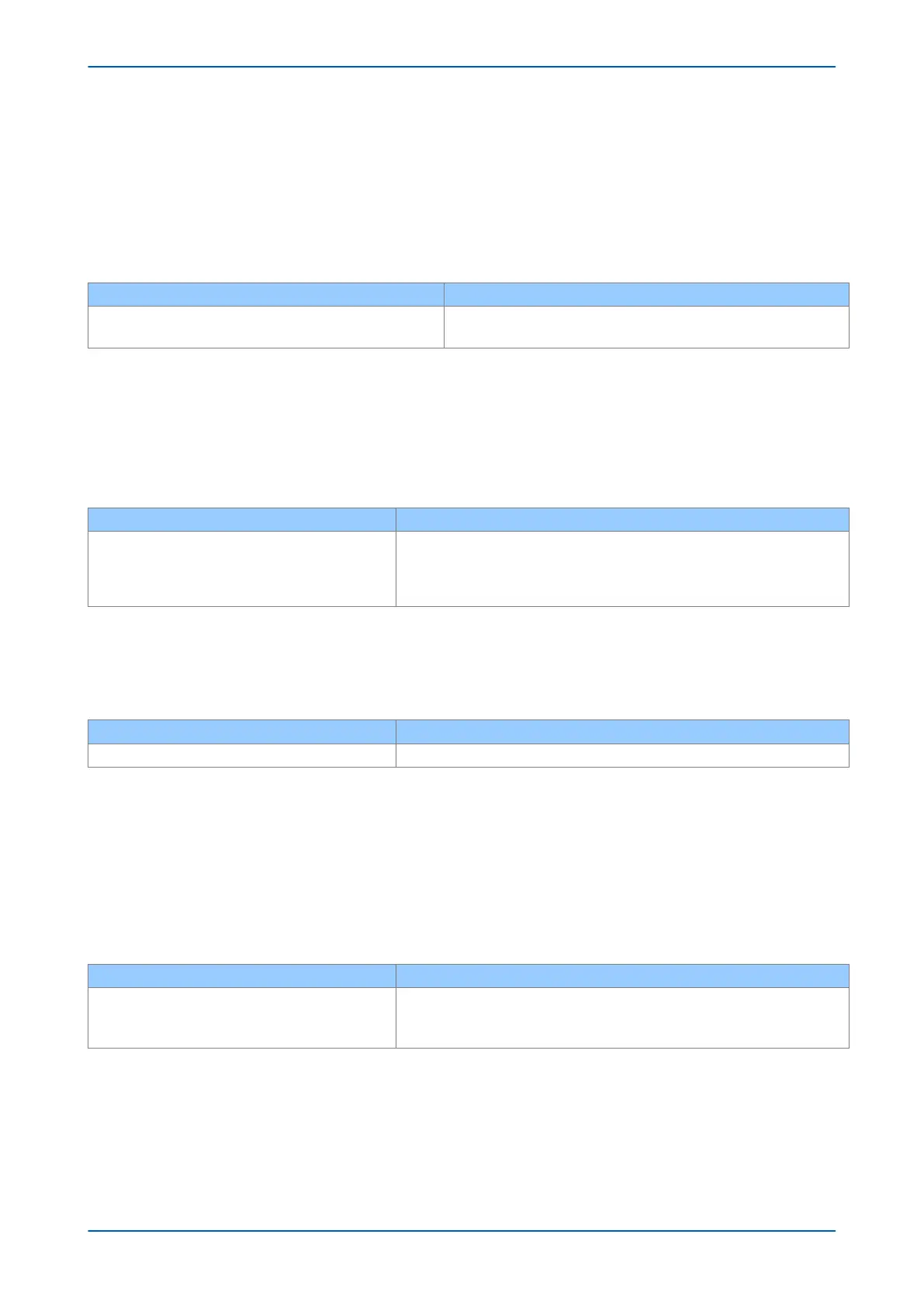
Power utility responsibilities: General Electric's contribution:
Create the list of the assets
We can help the power utilities to create this asset register automatically.
We can provide audits to list the Cyber assets
3.1.2 CIP 003
CIP 003 requires the implementation of a cyber-security policy, with associated documentation, which
demonstrates the management’s commitment and ability to secur
e its Critical Cyber Assets.
The standar
d also requires change control practices whereby all entity or vendor-related changes to hardware
and software components are documented and maintained.
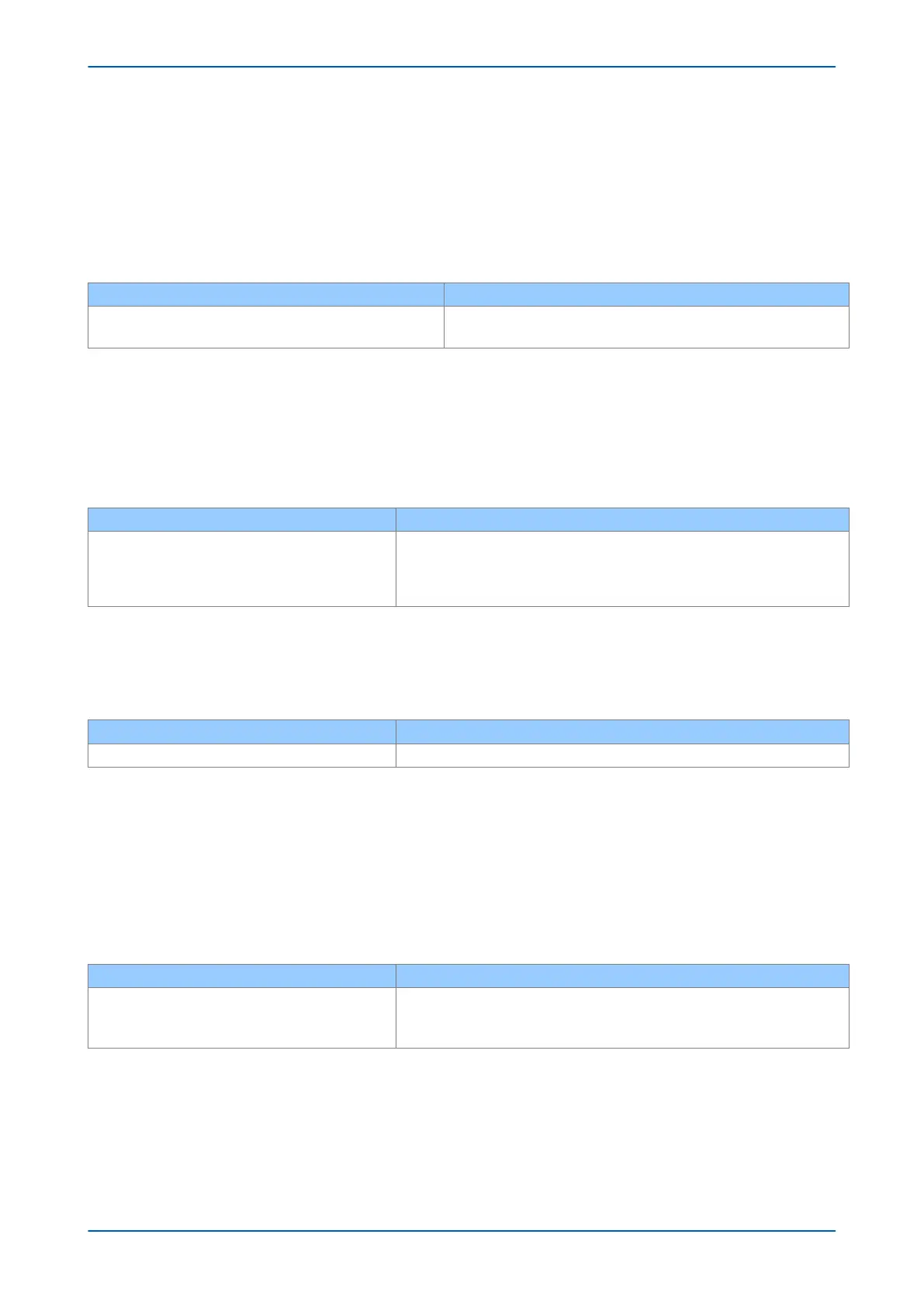
Power utility responsibilities: General Electric's contribution:
To create a Cyber-security Policy
We can help the power utilities to have access control to its critical assets by
providing centralized Access contr
ol.
We can help the customer with its change control by providing a section in the
documentation where it describes changes affecting the hardware and software.
3.1.3 CIP 004
CIP 004 requires that personnel with authorized cyber access or authorized physical access to Critical Cyber
Assets, (including contractors and ser
vice vendors), have an appropriate level of training.
Power utility responsibilities: General Electric's contribution:
To provide appropriate training of its personnel We can provide cyber-security training
3.1.4 CIP 005
CIP 005 requires the establishment of an Electronic Security Perimeter (ESP), which provides:
● The disabling of por
ts and ser
vices that are not required
● Permanent monitoring and access to logs (24x7x365)
● Vulnerability Assessments (yearly at a minimum)
● Documentation of Network Changes
Power utility responsibilities: General Electric's contribution:
To monitor access to the ESP
To per
form the vulnerability assessments
To document network changes
To disable all ports not used in the IED
To monitor and record all access to the IED
3.1.5 CIP 006
CIP 006 states that Physical Security controls, providing perimeter monitoring and logging along with robust
access contr
ols, must be implemented and documented. All cyber assets used for Physical Security are consider
ed
critical and should be treated as such:
Chapter 19 - Cyber-Security P14x
460 P14xEd1-TM-EN-1

 Loading...
Loading...