10-55
Catalyst 3750-X and 3560-X Switch Software Configuration Guide
OL-21521-01
Chapter 10 Configuring Switch-Based Authentication
Configuring the Switch for Secure Copy Protocol
Use the no ip http client secure-trustpoint name to remove a client trustpoint configuration. Use the
no ip http client secure-ciphersuite to remove a previously configured CipherSuite specification for
the client.
Displaying Secure HTTP Server and Client Status
To display the SSL secure server and client status, use the privileged EXEC commands in Table 10-7:
Configuring the Switch for Secure Copy Protocol
The Secure Copy Protocol (SCP) feature provides a secure and authenticated method for copying switch
configurations or switch image files. SCP relies on Secure Shell (SSH), an application and a protocol
that provides a secure replacement for the Berkeley r-tools.
For SSH to work, the switch needs an RSA public/private key pair. This is the same with SCP, which
reli
es on SSH for its secure transport.
Because SSH also relies on AAA authentication, and S
CP relies further on AAA authorization, correct
configuration is necessary.
• Before enabling SCP, you must correctly configure SSH, authentication, and authorization on the
switch.
• Because SCP relies on SSH for its secure transport, the router must have an Rivest, Shamir, and
Adelman (RSA) key pair.
Note When using SCP, you cannot enter the password into the copy command. You must enter the password
when prompted.
Step 3
ip http client secure-ciphersuite
{[3des-ede-cbc-sha] [rc4-128-md5]
[rc4-128-sha] [des-cbc-sha]}
(Optional) Specify the CipherSuites (encryption algorithms) to be used
for encryption over the HTTPS connection. If you do not have a reason to
specify a particular CipherSuite, you should allow the server and client to
negotiate a CipherSuite that they both support. This is the default.
Step 4
end Return to privileged EXEC mode.
Step 5
show ip http client secure status Display the status of the HTTP secure server to verify the configuration.
Step 6
copy running-config startup-config (Optional) Save your entries in the configuration file.
Command Purpose
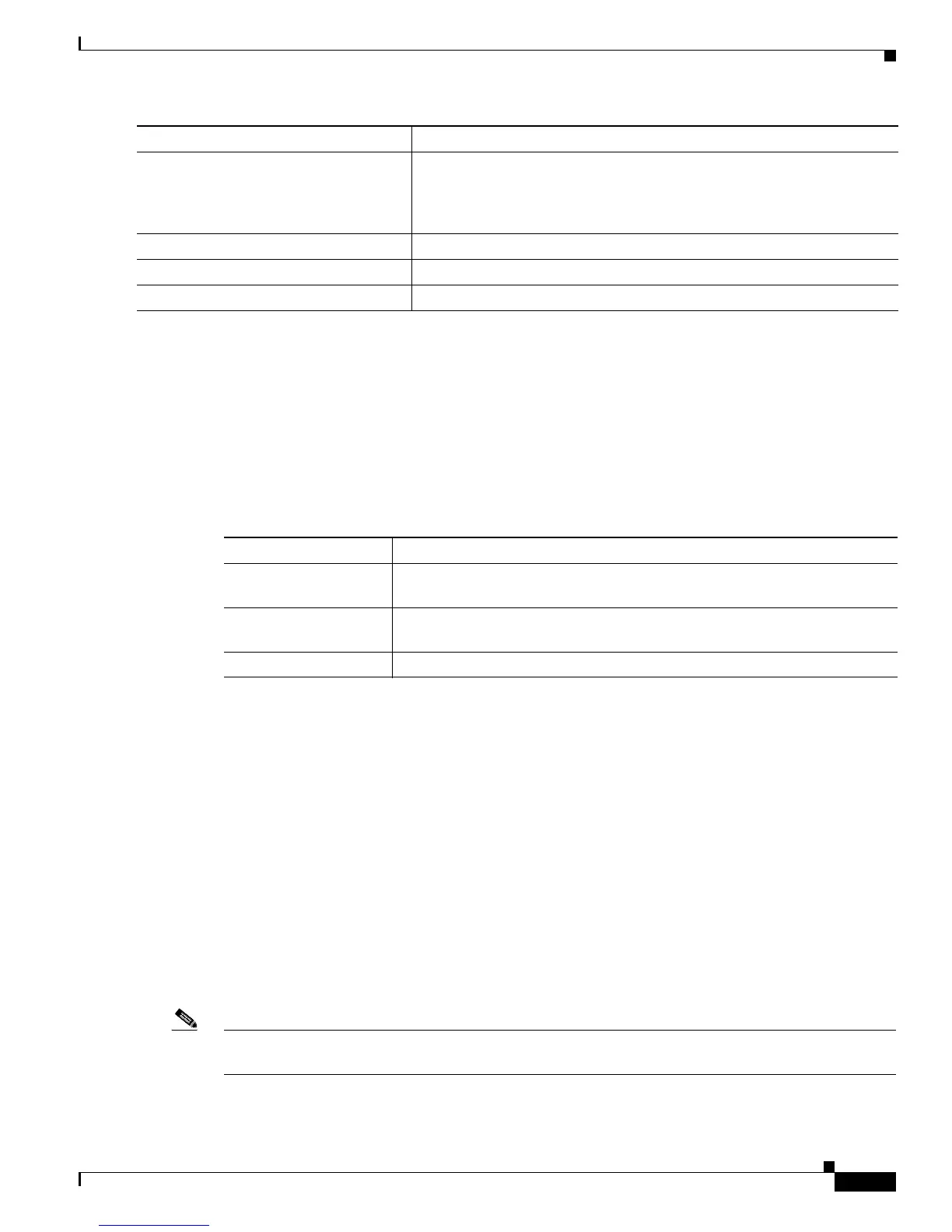
Ta ble 10-7 Commands for Displaying the SSL Secure Server and Client Status
Command Purpose
show ip http client
se
cure status
Shows the HTTP secure client configuration.
show ip http server
se
cure status
Shows the HTTP secure server configuration.
show running-config Shows the generated self-signed certificate for secure HTTP co
nnections.
 Loading...
Loading...