7-28
Using Passwords, Port Security, and Authorized IP Managers To Protect Against Unauthorized Access
Configuring and Monitoring Port Security
Using Passwords, Port
Security, and Authorized IP
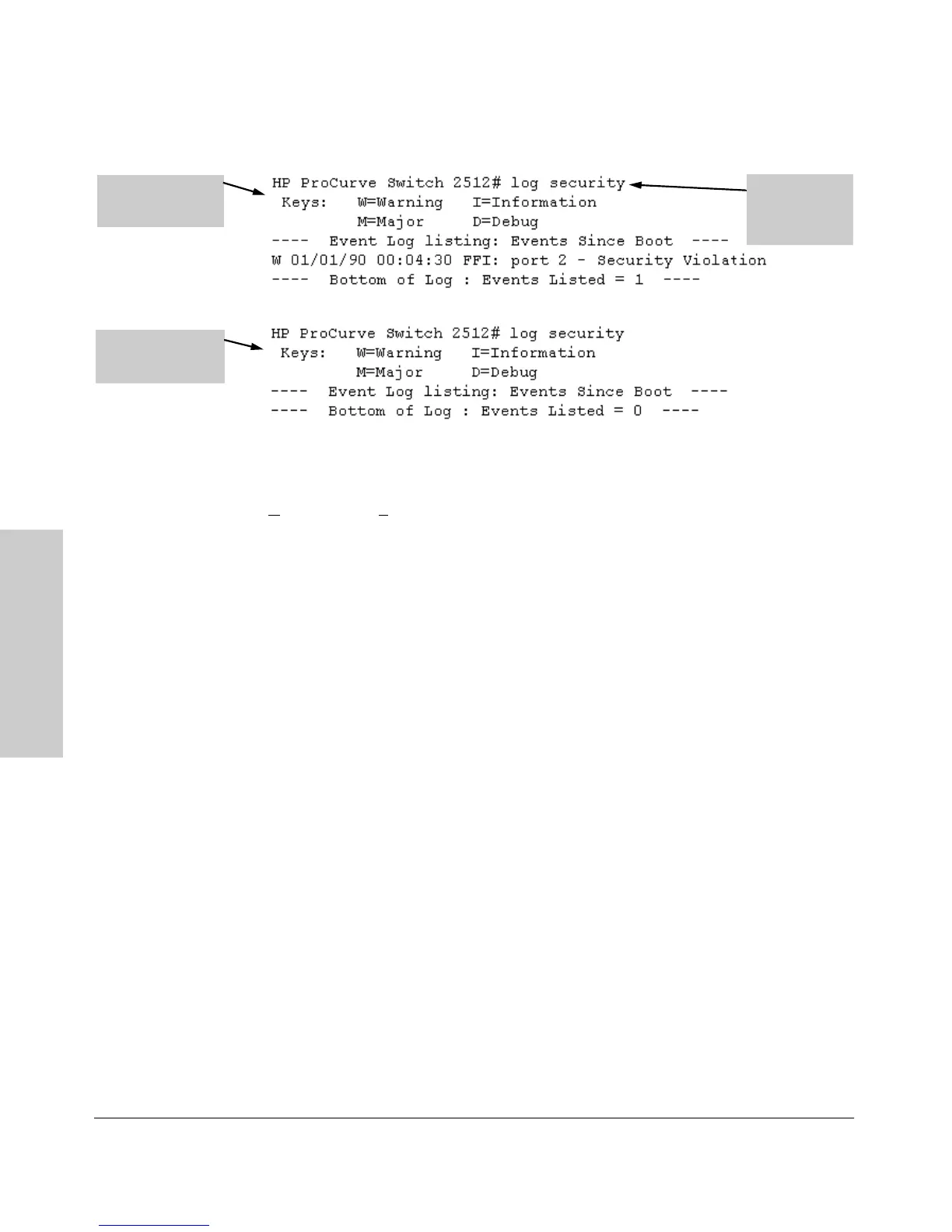
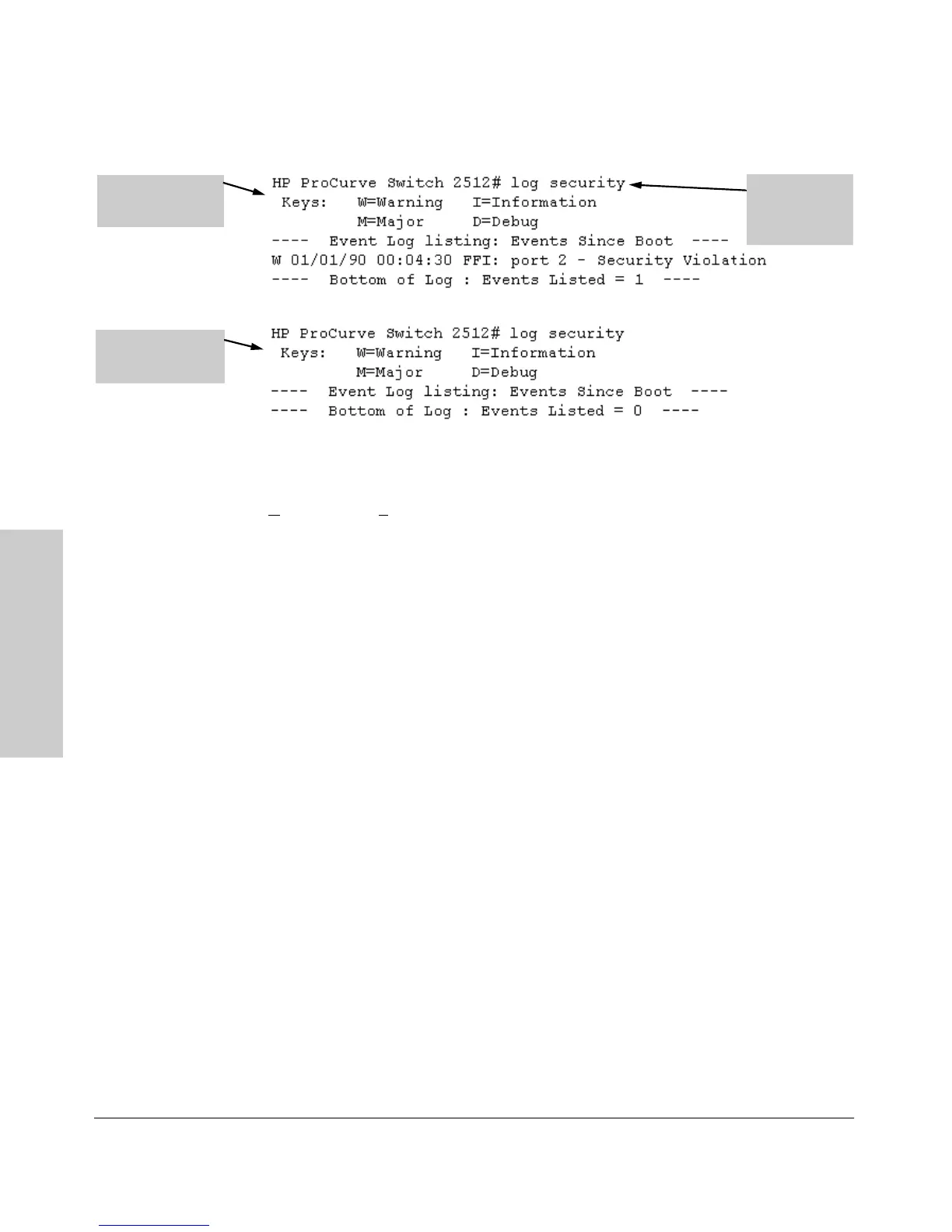
Figure 7-12. Example of Log Listing With and Without Detected Security Violation
From the Menu Interface: In the Main Menu, click on
4. Event Log and use
N
ext page and Prev page to review the Event Log contents.
For More Event Log Information. See “Using the Event Log To Identify
Problem Sources” on page 11-11.
Web: Checking for Intrusions, Listing Intrusion Alerts, and
Resetting Alert Flags
1. Check the Alert Log by clicking on the Status tab and the [Overview] button.
If there is a “Security Violation” entry, do the following:
a. Click on the Security tab.
b. Click on [Intrusion Log]. “Ports with Intrusion Flag” indicates any ports
for which the alert flag has not been cleared.
c. To clear the current alert flags, click on [Reset Alert Flags].
To access the web-based Help provided for the switch, click on [?] in the web
browser screen.
Operating Notes for Port Security
Identifying the IP Address of an Intruder. The Intrusion Log lists
detected intruders by MAC address. If you are using HP TopTools for Hubs &
Switches to manage your network, you can use the TopTools inventory reports
to link MAC addresses to their corresponding IP addresses. (Inventory reports
are organized by device type; hubs, switches, servers, etc.)
Log Listing with
Security Violation
Detected
Log Listing with No
Security Violation
Detected
Log Command
with
“security” for
Search String
 Loading...
Loading...