135
Cisco 3900 Series, Cisco 2900 Series, and Cisco 1900 Series Integrated Services Routers Generation 2 Software Configuration Guide
Chapter Configuring Security Features
Configuring VPN
Configure the IKE Policy
To configure the Internet Key Exchange (IKE) policy, follow these steps, beginning in global
configuration mode.
SUMMARY STEPS
1. crypto isakmp policy priority
2. encryption {des | 3des | aes | aes 192 | aes 256}
3. hash {md5 | sha}
4. authentication {rsa-sig | rsa-encr | pre-share}
5. group {1 | 2 | 5}
6. lifetime seconds
7. exit
8.
DETAILED STEPS
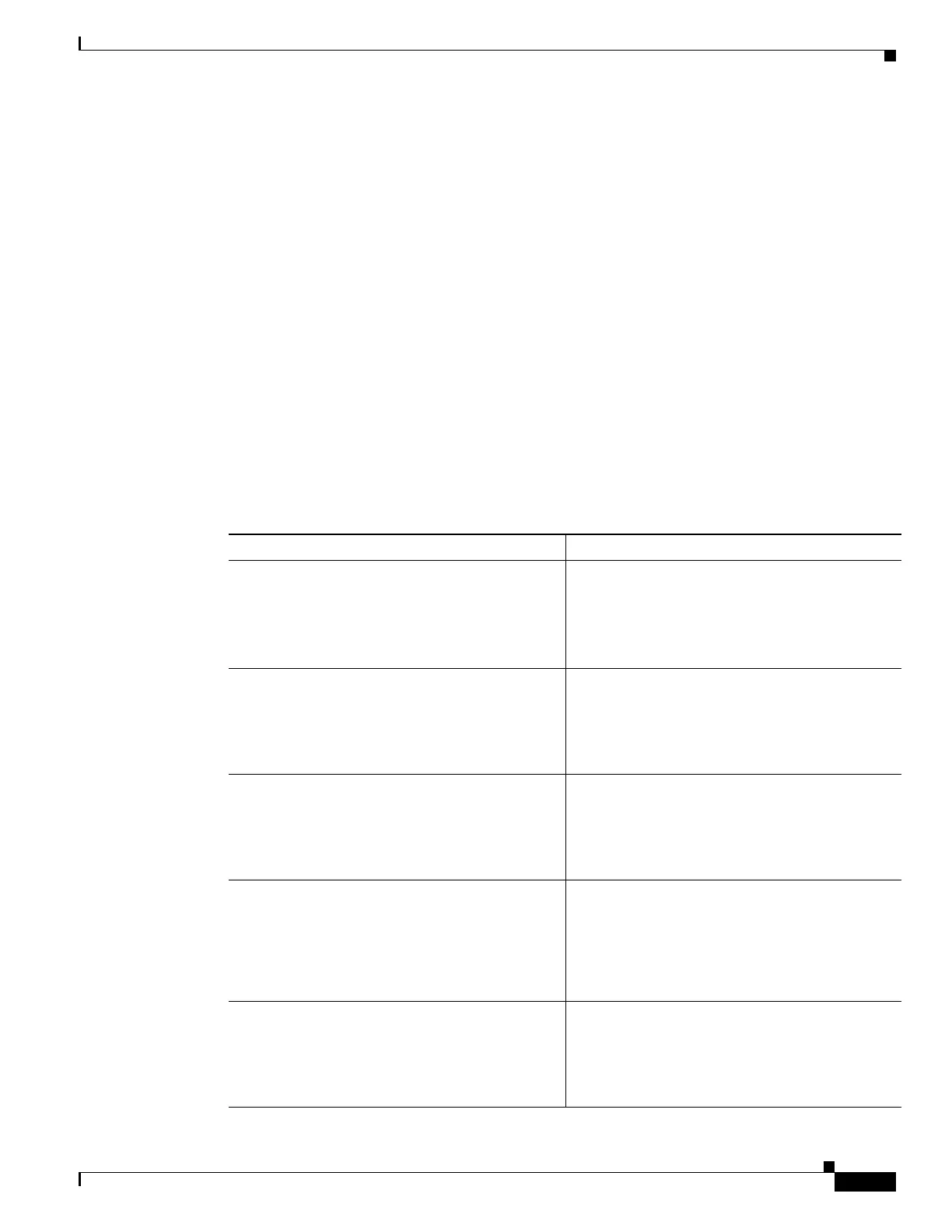
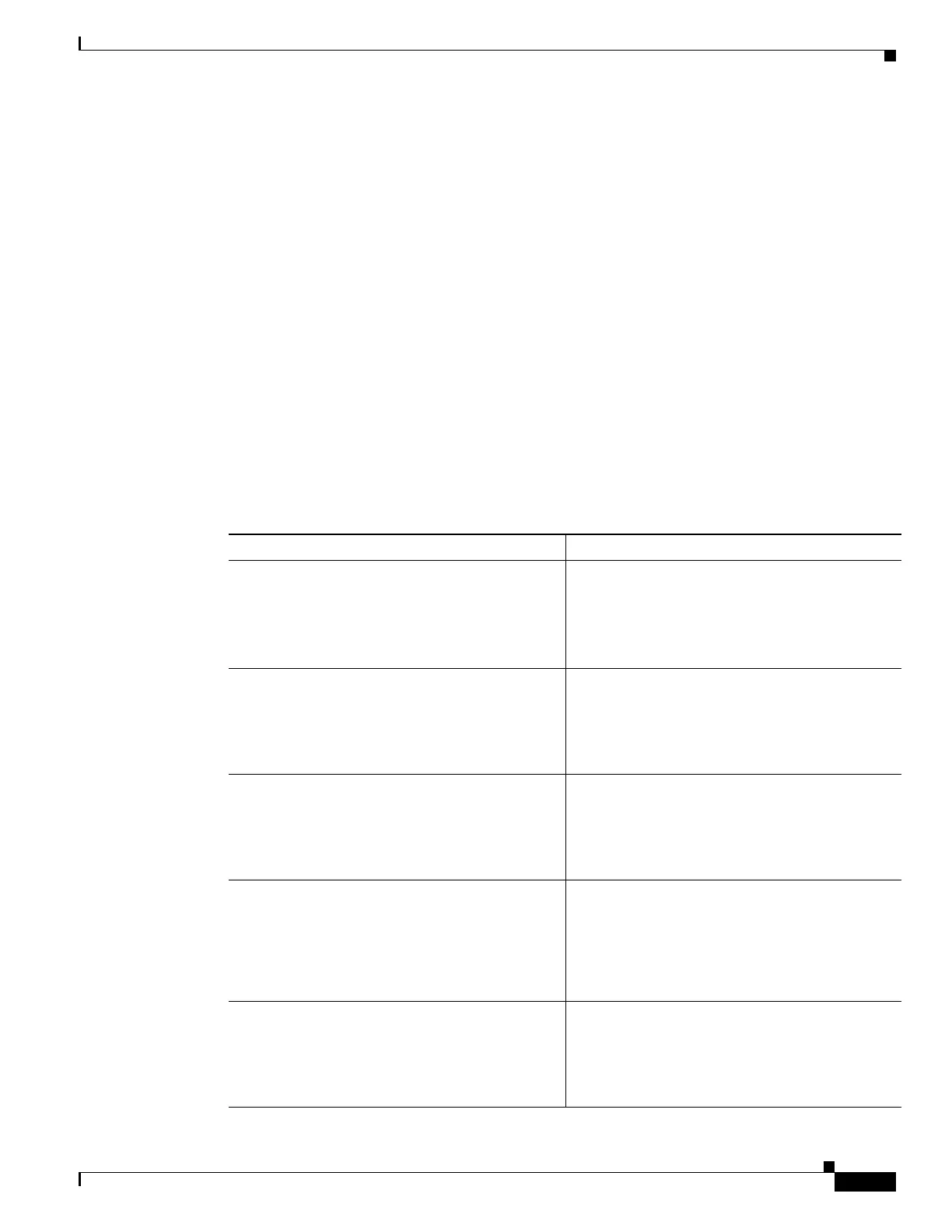
Command or Action Purpose
Step 1
crypto isakmp policy priority
Example:
Router(config)# crypto isakmp policy 1
Router(config-isakmp)#
Creates an IKE policy that is used during IKE
negotiation. The priority is a number from 1 to
10000, with 1 being the highest.
Also enters the ISAKMP
1
policy configuration
mode.
Step 2
encryption {des | 3des | aes | aes 192 | aes 256}
Example:
Router(config-isakmp)# encryption 3des
Router(config-isakmp)#
Specifies the encryption algorithm used in the IKE
policy.
The example specifies 168-bit DES
2
.
Step 3
hash {md5 | sha}
Example:
Router(config-isakmp)# hash md5
Router(config-isakmp)#
Specifies the hash algorithm used in the IKE
policy.
The example specifies the MD5
3
algorithm. The
default is SHA-1
4
.
Step 4
authentication {rsa-sig | rsa-encr | pre-share}
Example:
Router(config-isakmp)# authentication
pre-share
Router(config-isakmp)#
Specifies the authentication method used in the
IKE policy.
The example specifies a pre-shared key.
Step 5
group {1 | 2 | 5}
Example:
Router(config-isakmp)# group 2
Router(config-isakmp)#
Specifies the Diffie-Hellman group to be used in
an IKE policy.
 Loading...
Loading...