78
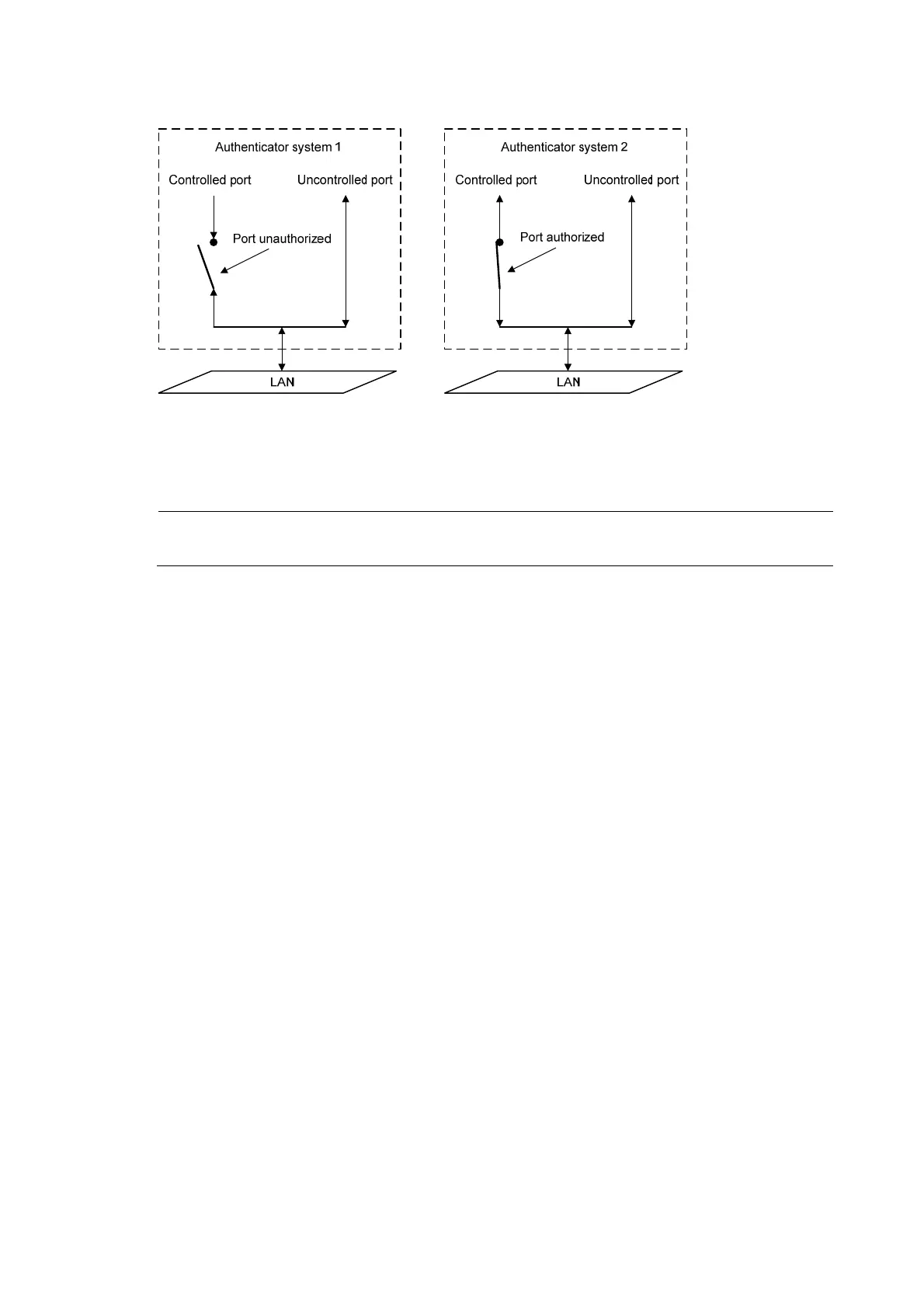
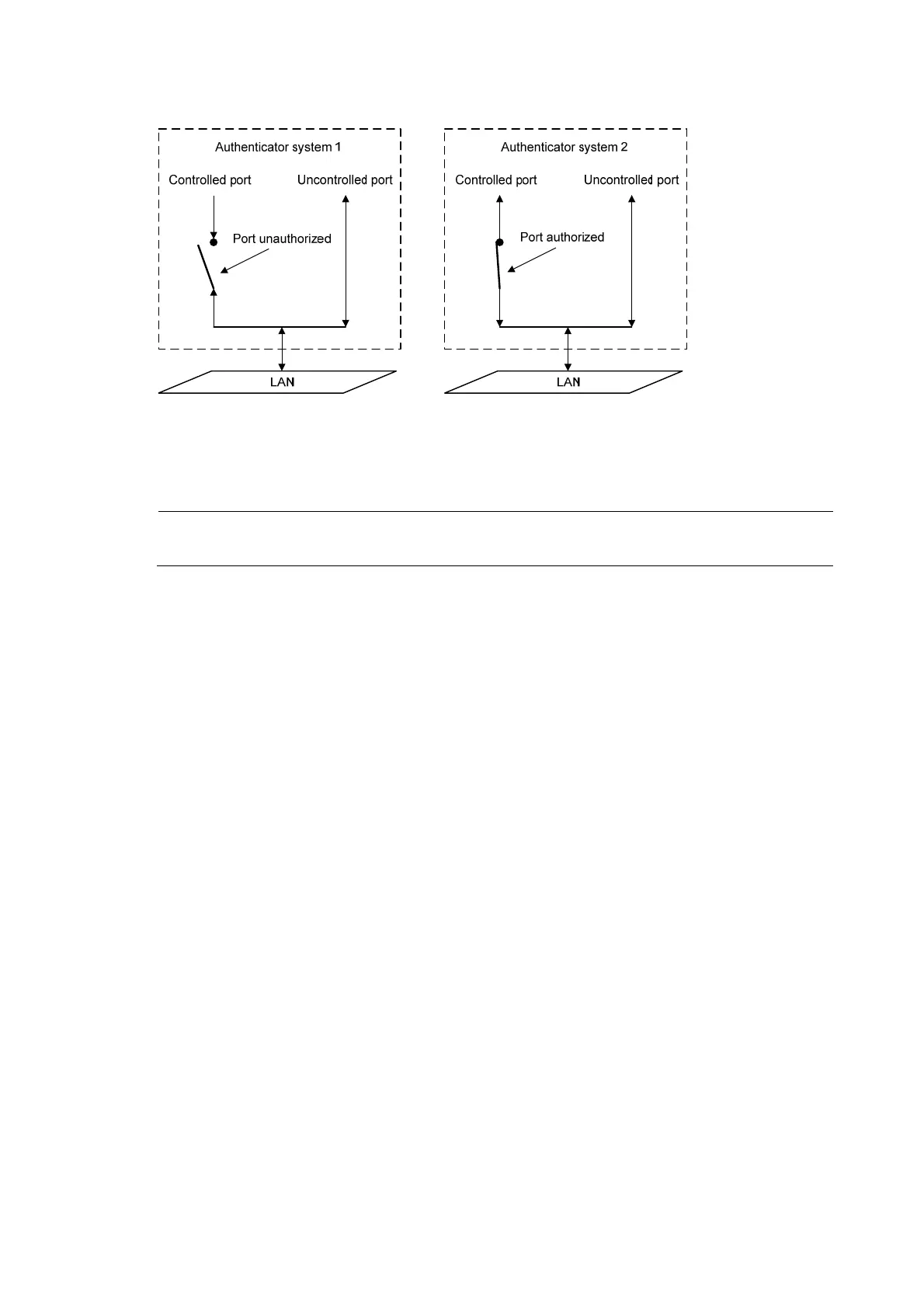
Figure 35 Authorization state of a controlled port
In the unauthorized state, a controlled port controls traffic in one of the following ways:
• Performs bidirectional traffic control to deny traffic to and from the client.
• Performs unidirectional traffic control to deny traffic from the client.
NOTE:
The HP devices support only unidirectional traffic control.
802.1X-related protocols
802.1X uses the Extensible Authentication Protocol (EAP) to transport authentication information for the
client, the network access device, and the authentication server. EAP is an authentication framework that
uses the client/server model. It supports a variety of authentication methods, including MD5-Challenge,
EAP-Transport Layer Security (EAP-TLS), and Protected EAP (PEAP).
802.1X defines EAP over LAN (EAPOL) for passing EAP packets between the client and the network
access device over a wired or wireless LAN. Between the network access device and the authentication
server, 802.1X delivers authentication information in one of the following methods:
• Encapsulates EAP packets in RADIUS by using EAP over RADIUS (EAPOR), as described in “EAP
re
l
ay.”
• Extracts authentication information from the EAP packets and encapsulates the information in
standard RADIUS packets, as described in “EAP termination.”
 Loading...
Loading...