1-18
Cisco ASA Series CLI Configuration Guide
Chapter 1 Configuring the Cisco Phone Proxy
Configuring the Phone Proxy
Step 6 While configuring the phone proxy instance (in the Phone Proxy Configuration mode), enter the
following command to configure the mode of the cluster to be mixed mode because the default is
nonsecure:
hostname(config-phone-proxy)# cluster-mode mixed
Step 7 Enable the phone proxy y with SIP and Skinny inspection. See Enabling the Phone Proxy with SIP and
Skinny Inspection, page 1-26.
Creating Trustpoints and Generating Certificates
Create trustpoints and generate certificates for each entity in the network (Cisco UCM, Cisco UCM and
TFTP, TFTP server, CAPF) that the IP phone must trust. The certificates are used in creating the CTL
file.
You need to create trustpoints for each Cisco UCM (primary and secondary if a secondary Cisco UCM
is used) and TFTP server in the network. The trustpoints need to be in the CTL file for the phones to
trust the Cisco UCM.
Prerequisites
Import the required certificates, which are stored on the Cisco UCM. See Certificates from the Cisco
UCM, page 1-7 and Importing Certificates from the Cisco UCM, page 1-15.
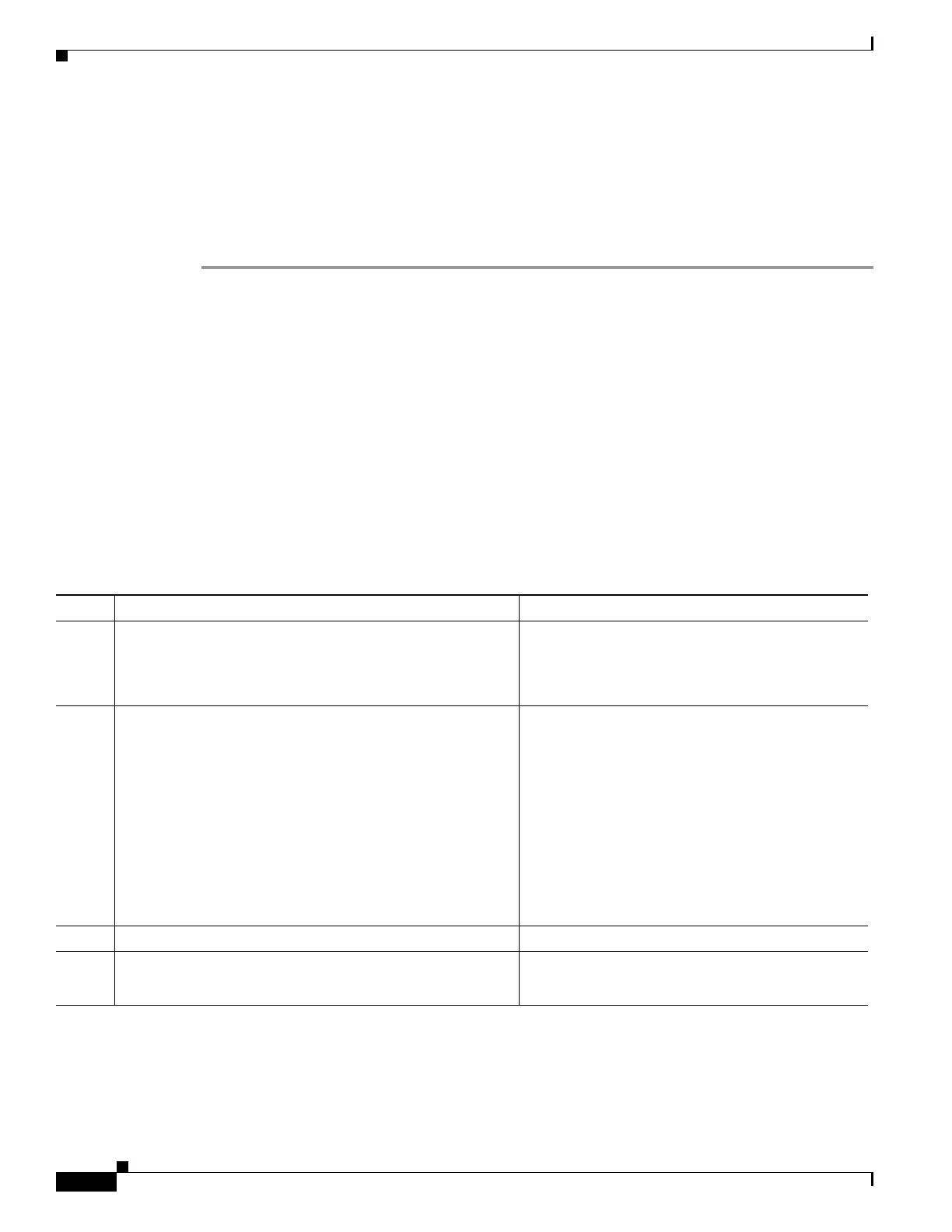
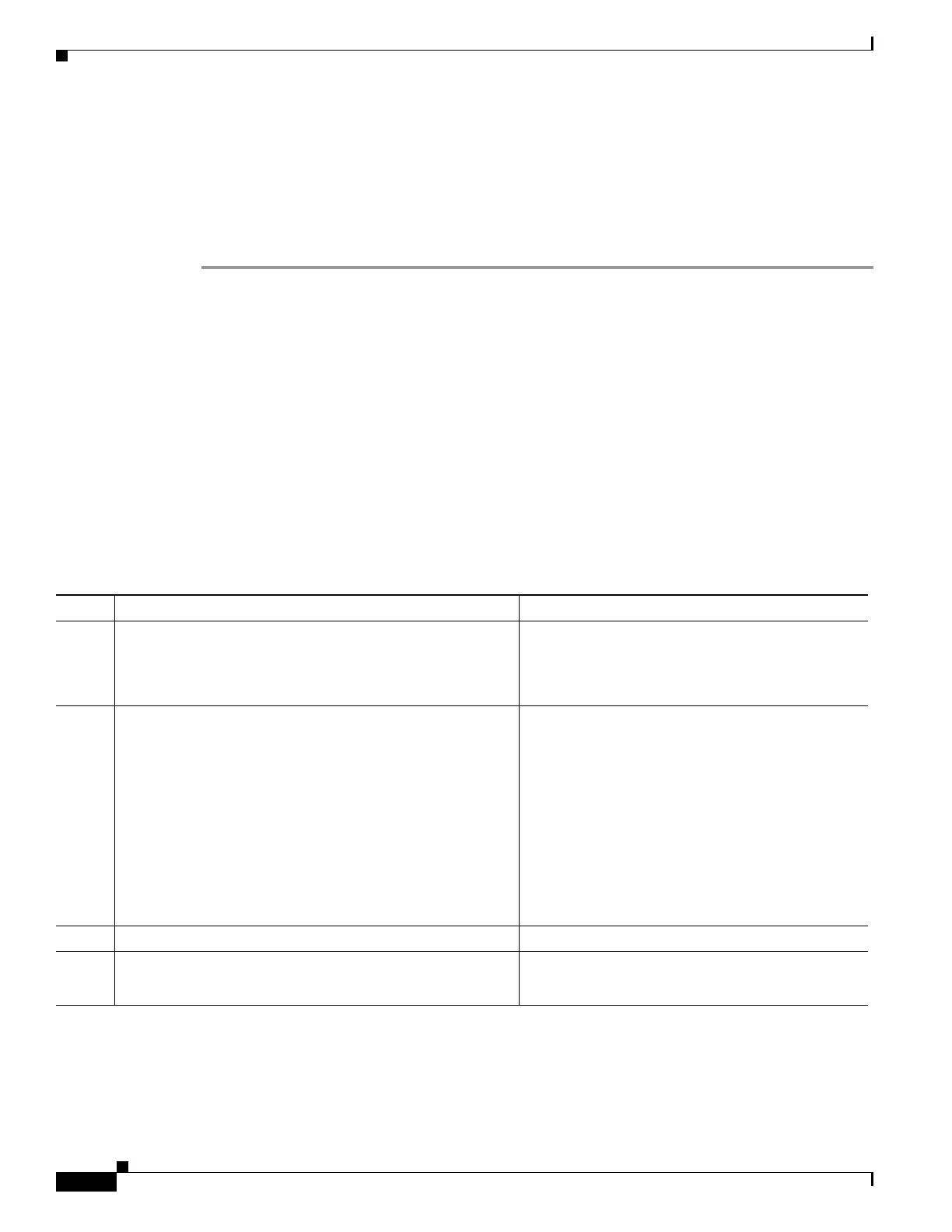
Command Purpose
Step 1
hostname(config)# crypto key generate rsa label
key-pair-label modulus size
Example:
crypto key generate rsa label cucmtftp_kp modulus
1024
Creates a keypair that can be used for the trustpoints.
Step 2
hostname(config)# crypto ca trustpoint
trustpoint_name
Example:
crypto ca trustpoint cucm_tftp_server
Creates the trustpoints for each entity in the network
(primary Cisco UCM, secondary Cisco UCM, and
TFTP server).
Note You are only required to create a separate
trustpoint for the TFTP server when the
TFTP server resides on a different server
from the Cisco UCM. See Example 3:
Mixed-mode Cisco UCM cluster, Cisco
UCM and TFTP Server on Different Servers,
page 1-47 for an example of this
configuration.
Step 3
hostname(config-ca-trustpoint)# enrollment self
Generates a self-signed certificate.
Step 4
hostname(config-ca-trustpoint)# keypair keyname
Example:
keypair cucmtftp_kp
Specifies the keypair whose public key is being
certified.

 Loading...
Loading...