1-5
Cisco ASA Series CLI Configuration Guide
Chapter 1 Configuring Access Rules
Information About Access Rules
For connectionless protocols such as ICMP, however, the ASA establishes unidirectional sessions, so
you either need access rules to allow ICMP in both directions (by applying access lists to the source and
destination interfaces), or you need to enable the ICMP inspection engine. The ICMP inspection engine
treats ICMP sessions as bidirectional connections. To control ping, specify echo-reply (0) (ASA to host)
or echo (8) (host to ASA).
Allowing Broadcast and Multicast Traffic through the Transparent Firewall Using Access
Rules
In routed firewall mode, broadcast and multicast traffic is blocked even if you allow it in an access rule,
including unsupported dynamic routing protocols and DHCP (unless you configure DHCP relay).
Transparent firewall mode can allow any IP traffic through.
Note Because these special types of traffic are connectionless, you need to apply an access rule to both
interfaces, so returning traffic is allowed through.
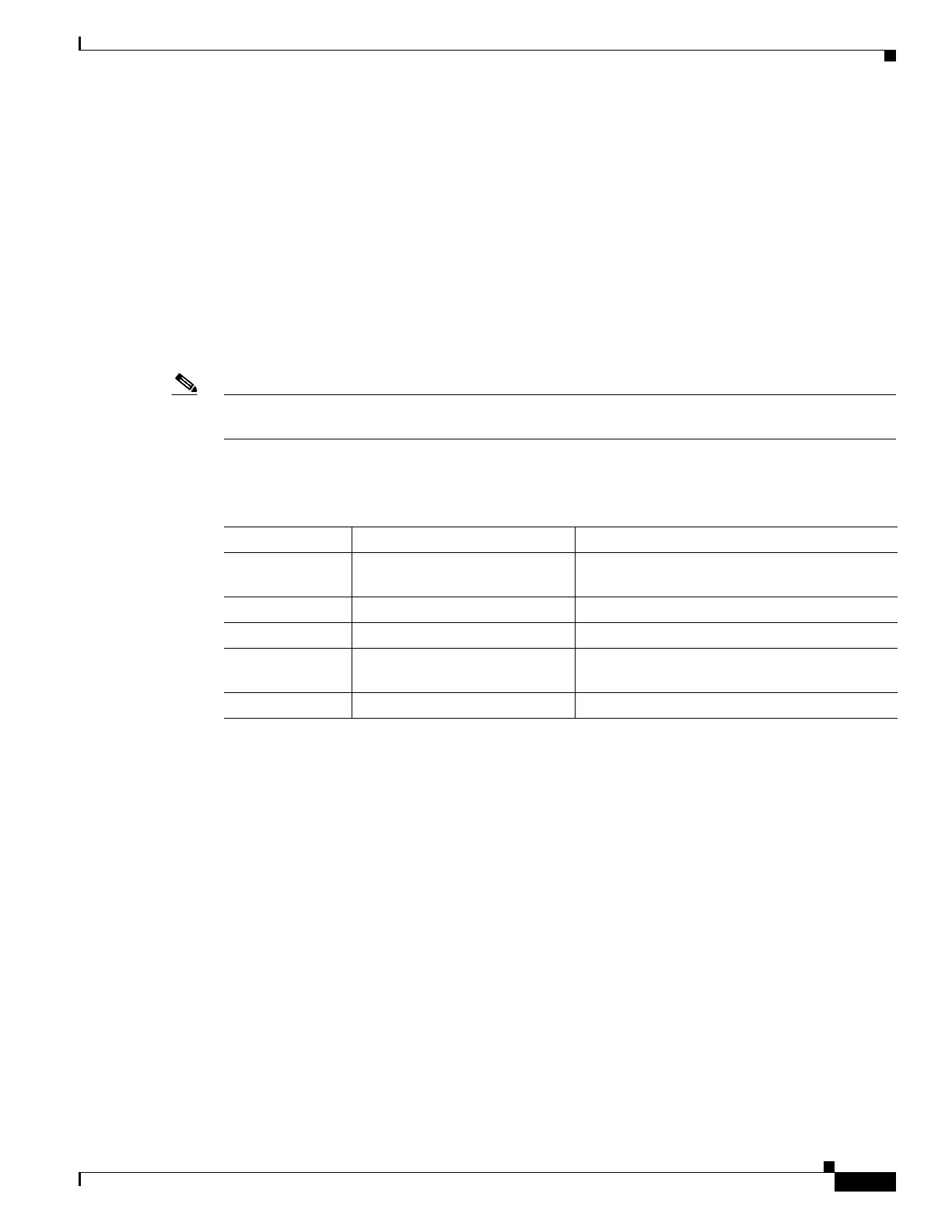
Table 1-1 lists common traffic types that you can allow through the transparent firewall.
Management Access Rules
You can configure access rules that control management traffic destined to the ASA. Access control rules
for to-the-box management traffic (defined by such commands as http, ssh, or telnet) have higher
precedence than an management access rule applied with the control-plane option. Therefore, such
permitted management traffic will be allowed to come in even if explicitly denied by the to-the-box
access list.
Information About EtherType Rules
This section describes EtherType rules and includes the following topics:
• Supported EtherTypes and Other Traffic, page 1-6
• Access Rules for Returning Traffic, page 1-6
• Allowing MPLS, page 1-6
Table 1-1 Transparent Firewall Special Traffic
Traffic Type Protocol or Port Notes
DHCP UDP ports 67 and 68 If you enable the DHCP server, then the ASA
does not pass DHCP packets.
EIGRP Protocol 88 —
OSPF Protocol 89 —
Multicast streams The UDP ports vary depending
on the application.
Multicast streams are always destined to a
Class D address (224.0.0.0 to 239.x.x.x).
RIP (v1 or v2) UDP port 520 —
 Loading...
Loading...