580
Configuring QoS
Understanding QoS
Classification Based on QoS ACLs
Packets can also be classified in input policy maps based on an ACL lookup. The ACL classification is communicated to
an output policy by assigning a QoS group or number in the input policy map. To classify based on ACL lookup, you first
create an IP or MAC ACL. Configure a class map and use the match access-group {acl-number | acl name} class-map
configuration command, and attach the class map to a policy map.
Note: You cannot configure match access-group for an output policy map.
You can use IP standard, IP extended, or Layer 2 MAC ACLs to define a group of packets with the same characteristics
(a class). You use the access-list global configuration command to configure IP ACLS to classify IP traffic based on Layer
3 and Layer 4 parameters. You use the mac access-list extended global configuration command to configure Layer 2
MAC ACLs to classify IP and non-IP traffic based on Layer 2 parameters.
Note: You cannot match IP fragments against configured IP extended ACLs to enforce QoS. IP fragments are sent as
best-effort. IP fragments are denoted by fields in the IP header.
You can use only ACLs with a permit action in a match access-group command. ACLs with a deny action are never
matched in a QoS policy.
Note: Only one access-group is supported per class for an input policy map.
Classification Based on QoS Groups
A QoS group is an internal label used by the switch to identify packets as a members of a specific class. The label is not
part of the packet header and is restricted to the switch that sets the label. QoS groups provide a way to tag a packet
for subsequent QoS action without explicitly marking (changing) the packet. You can then communicate an ACL match
from an input policy map to an output policy map.
A QoS group is identified at ingress and used at egress; it is assigned in an input policy to identify packets in an output
policy. See on page 580. The QoS groups help aggregate different classes of input traffic for a specific action in an
output policy.
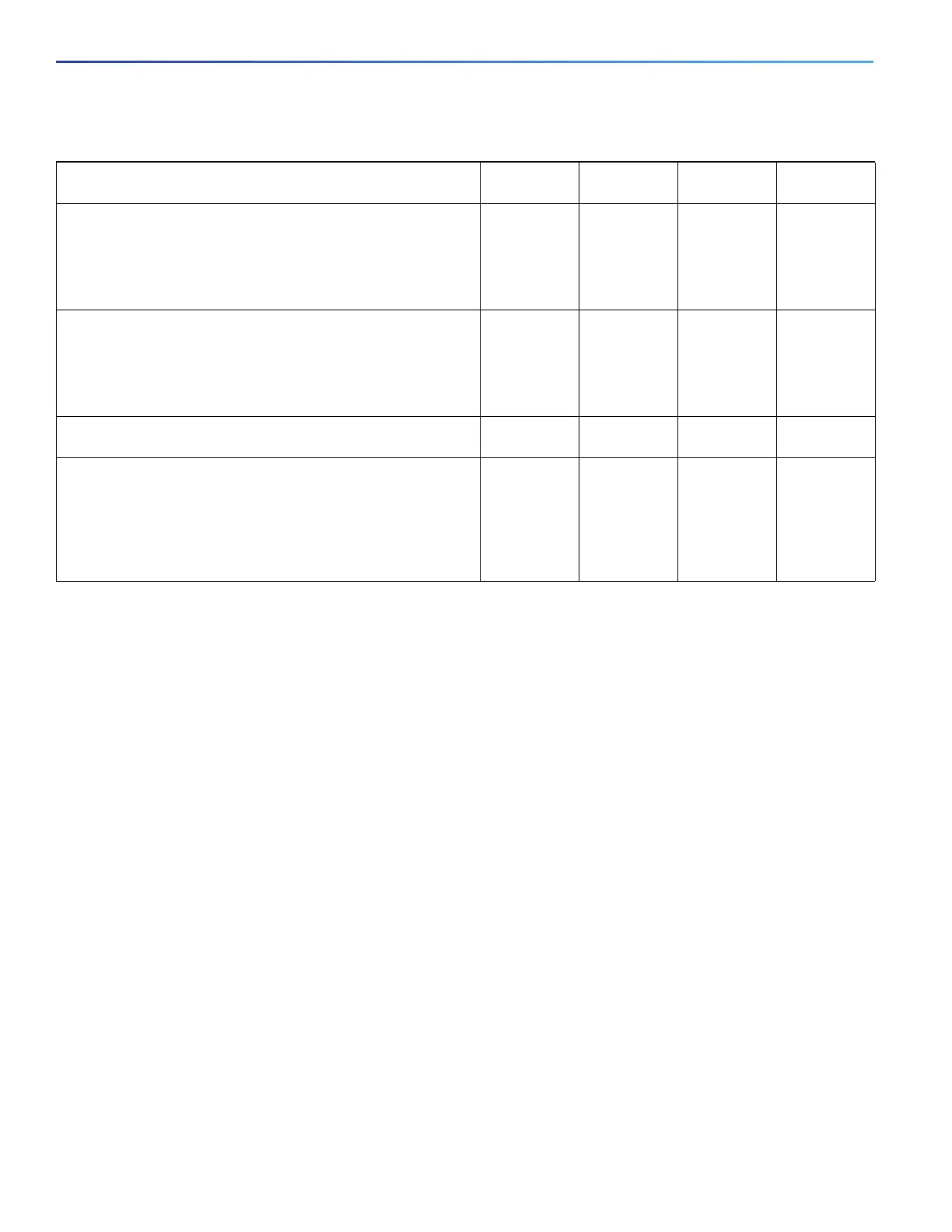
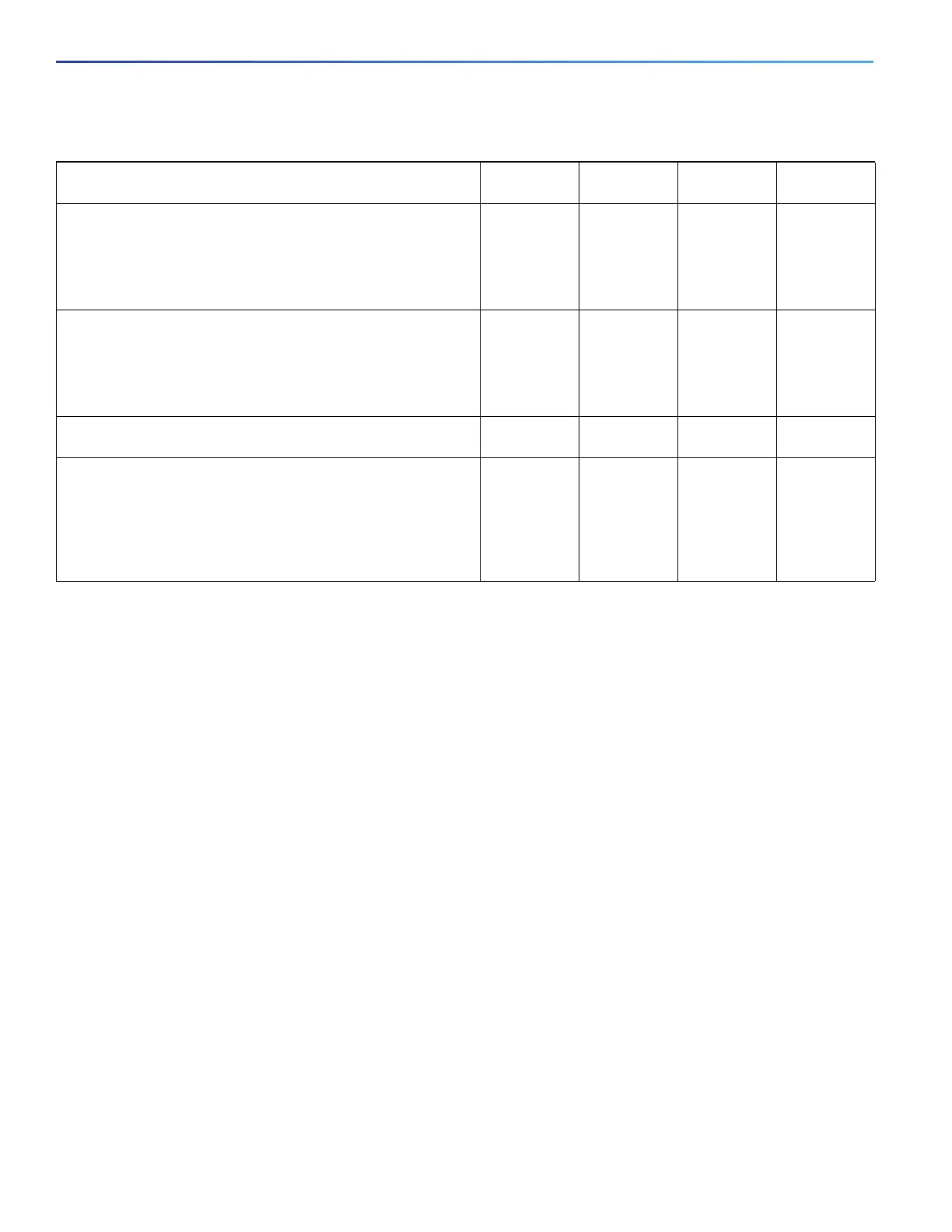
Mission critical date (gold data)—delay-sensitive applications
critical to the operation of an enterprise.
Level 1
Level 2
Level 3
AF21
AF22
AF23
18
20
22
2
2
2
2
2
2
Less critical data (silver data)—noncritical, but relatively
important data.
Level 1
Level 2
Level 3
AF11
AF12
AF13
10
12
14
1
1
1
1
1
1
Best-effort data (bronze data)—other traffic, including all
noninteractive traffic, regardless of importance.
Default 0 0 0
Less than best-effort data—noncritical, bandwidth-intensive
data traffic given the least preference. This is the first traffic type
to be dropped.
Level 1
Level 2
Level 3
2
4
6
0
0
0
0
0
0
Table 56 Typical Traffic Classifications (continued)
Traffic Type DSCP
per-hop
DSCP
(decimal)
IP
Precedence
CoS

 Loading...
Loading...