Chapter 7 Wireless
LTE Series User’s Guide
120
7.11.2 Additional Wireless Terms
The following table describes some WiFi network terms and acronyms used in the Zyxel Device’s Web
Configurator.
7.11.3 WiFi Security Overview
By their nature, radio communications are simple to intercept. For WiFi data networks, this means that
anyone within range of a WiFi network without security can not only read the data passing over the
airwaves, but also join the network. Once an unauthorized person has access to the network, he or she
can steal information or introduce malware (malicious software) intended to compromise the network.
For these reasons, a variety of security systems have been developed to ensure that only authorized
people can use a WiFi data network, or understand the data carried on it.
These security standards do two things. First, they authenticate. This means that only people presenting
the right credentials (often a username and password, or a “key” phrase) can access the network.
Second, they encrypt. This means that the information sent over the air is encoded. Only people with
the code key can understand the information, and only people who have been authenticated are
given the code key.
These security standards vary in effectiveness. Some can be broken, such as the old Wired Equivalent
Protocol (WEP). Using WEP is better than using no security at all, but it will not keep a determined
attacker out. Other security standards are secure in themselves but can be broken if a user does not use
them properly. For example, the WPA-PSK security standard is very secure if you use a long key which is
difficult for an attacker’s software to guess - for example, a twenty-letter long string of apparently
random numbers and letters - but it is not very secure if you use a short key which is very easy to guess -
for example, a three-letter word from the dictionary.
Because of the damage that can be done by a malicious attacker, it’s not just people who have
sensitive information on their network who should use security. Everybody who uses any WiFi network
should ensure that effective security is in place.
A good way to come up with effective security keys, passwords and so on is to use obscure information
that you personally will easily remember, and to enter it in a way that appears random and does not
include real words. For example, if your mother owns a 1970 Dodge Challenger and her favorite movie is
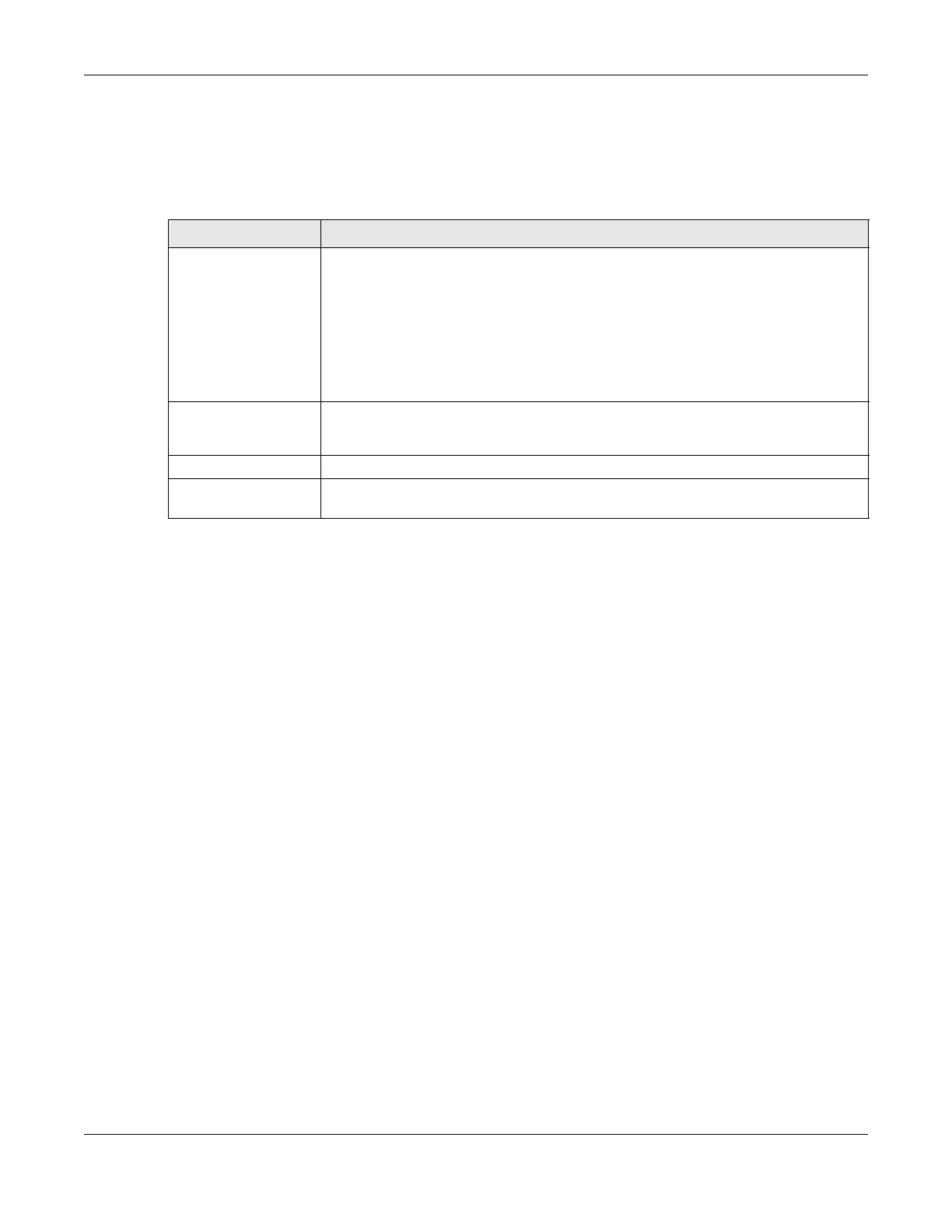
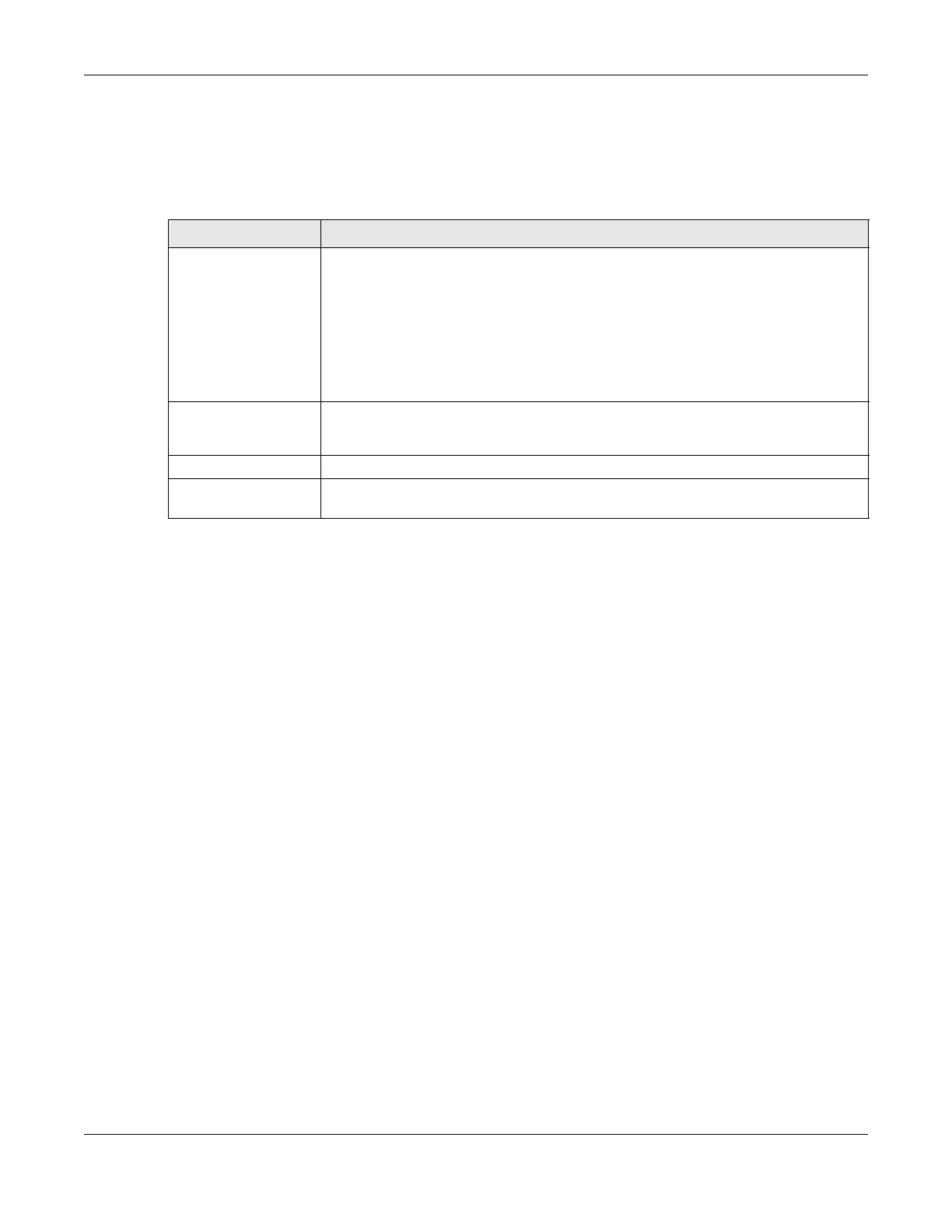
Table 39 Additional WiFi Terms
TERM DESCRIPTION
RTS/CTS Threshold In a WiFi network which covers a large area, WiFi devices are sometimes not aware of
each other’s presence. This may cause them to send information to the AP at the same
time and result in information colliding and not getting through.
By setting this value lower than the default value, the WiFi devices must sometimes get
permission to send information to the Zyxel Device. The lower the value, the more often
the devices must get permission.
If this value is greater than the fragmentation threshold value (see below), then WiFi
devices never have to get permission to send information to the Zyxel Device.
Preamble A preamble affects the timing in your WiFi network. There are two preamble modes: long
and short. If a device uses a different preamble mode than the Zyxel Device does, it
cannot communicate with the Zyxel Device.
Authentication The process of verifying whether a WiFi device is allowed to use the WiFi network.
Fragmentation
Threshold
A small fragmentation threshold is recommended for busy networks, while a larger
threshold provides faster performance if the network is not very busy.

 Loading...
Loading...