16-3
Cisco Security Appliance Command Line Configuration Guide
OL-10088-01
Chapter 16 Identifying Traffic with Access Lists
Access List Overview
Access Control Implicit Deny
Access lists have an implicit deny at the end of the list, so unless you explicitly permit it, traffic cannot
pass. For example, if you want to allow all users to access a network through the security appliance
except for particular addresses, then you need to deny the particular addresses and then permit all others.
IP Addresses Used for Access Lists When You Use NAT
When you use NAT, the IP addresses you specify for an access list depend on the interface to which the
access list is attached; you need to use addresses that are valid on the network connected to the interface.
This guideline applies for both inbound and outbound access lists: the direction does not determine the
address used, only the interface does.
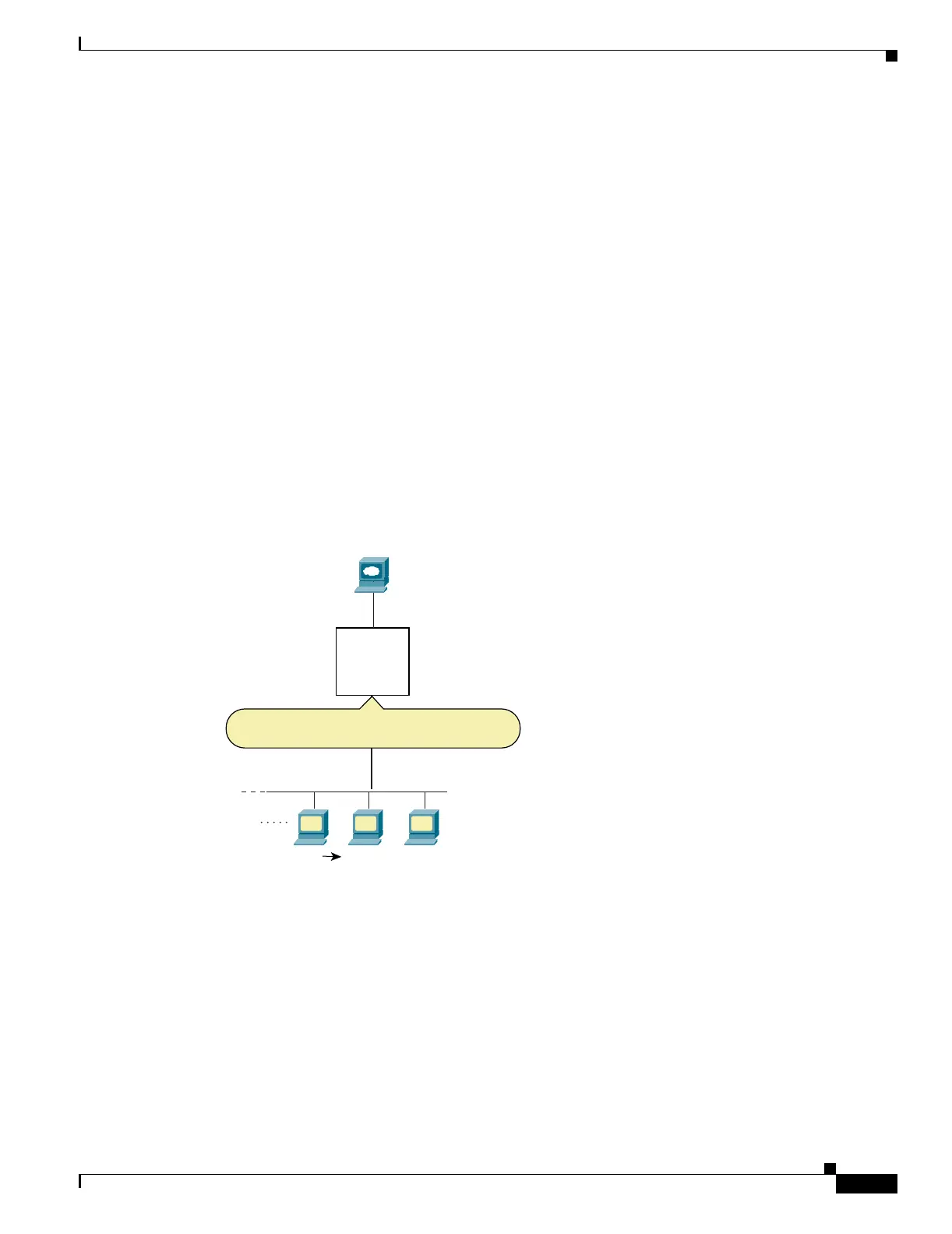
For example, you want to apply an access list to the inbound direction of the inside interface. You
configure the security appliance to perform NAT on the inside source addresses when they access outside
addresses. Because the access list is applied to the inside interface, the source addresses are the original
untranslated addresses. Because the outside addresses are not translated, the destination address used in
the access list is the real address (see Figure 16-1).
Figure 16-1 IP Addresses in Access Lists: NAT Used for Source Addresses
See the following commands for this example:
hostname(config)# access-list INSIDE extended permit ip 10.1.1.0 255.255.255.0 host
209.165.200.225
hostname(config)# access-group INSIDE in interface inside
209.165.200.225
Inside
Outside
Inbound ACL
Permit from 10.1.1.0/24 to 209.165.200.225
10.1.1.0/24
PAT
209.165.201.4:port10.1.1.0/24
104634
 Loading...
Loading...