17-33
Cisco Security Appliance Command Line Configuration Guide
OL-10088-01
Chapter 17 Applying NAT
NAT Examples
Overlapping Networks
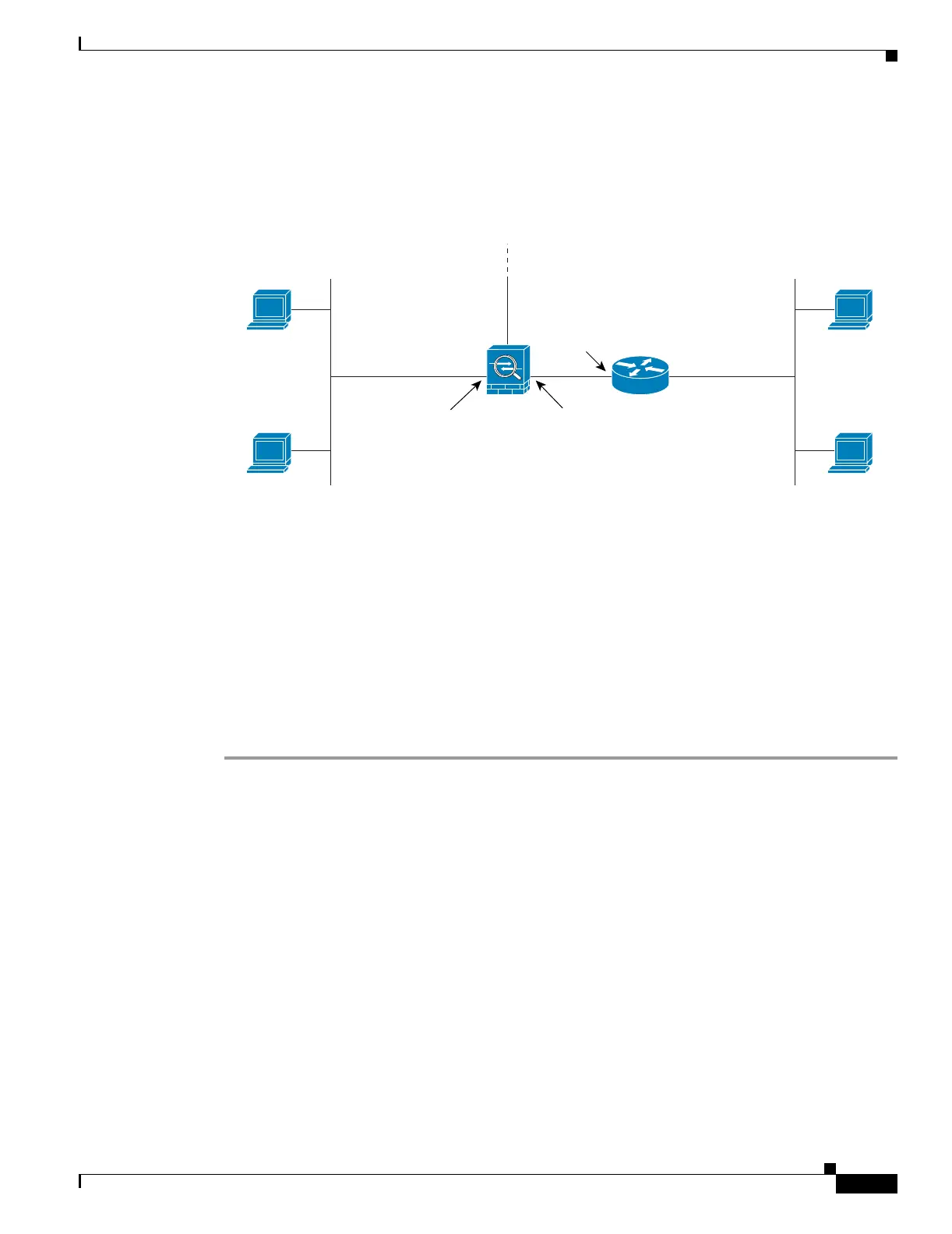
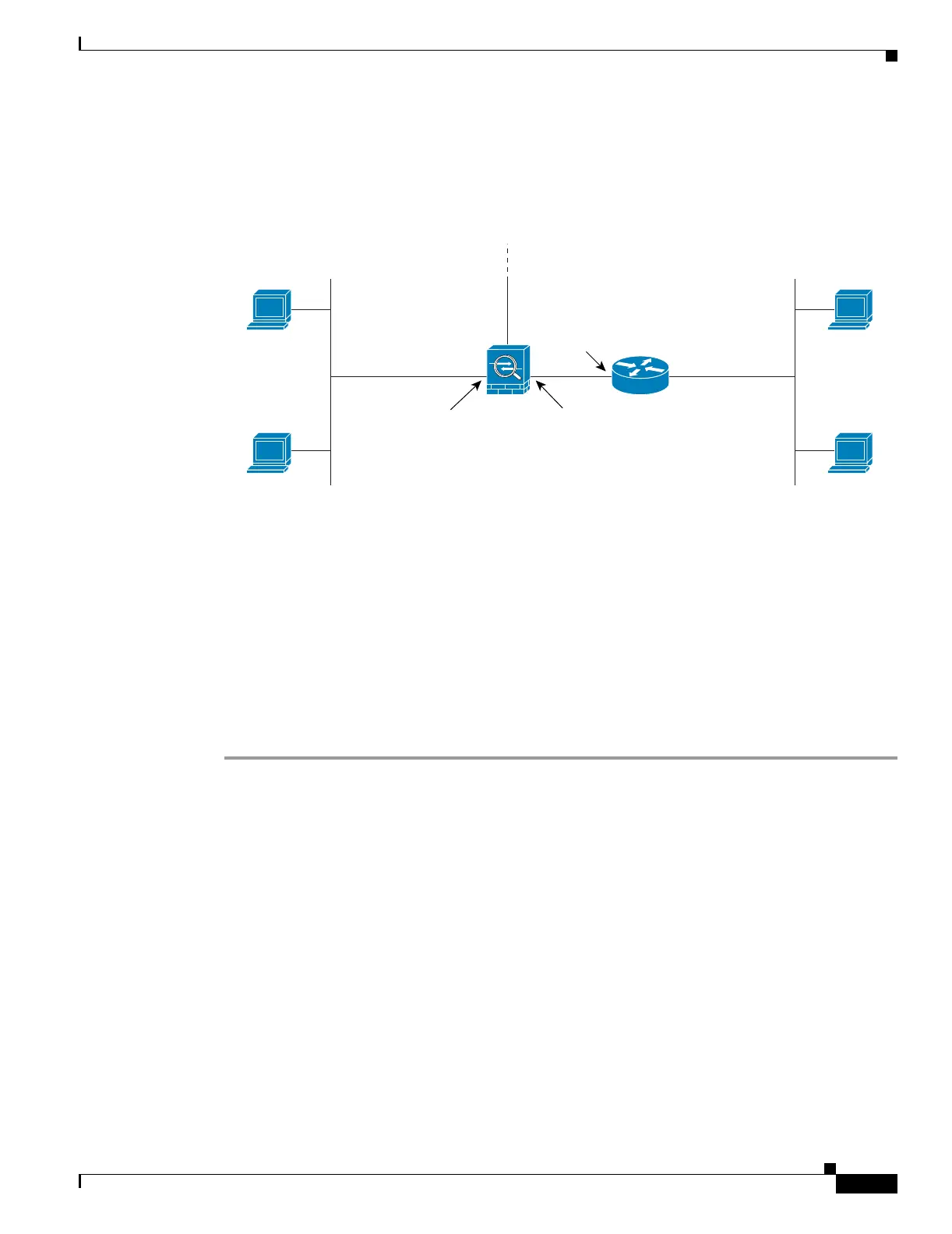
In Figure 17-26, the security appliance connects two private networks with overlapping address ranges.
Figure 17-26 Using Outside NAT with Overlapping Networks
Two networks use an overlapping address space (192.168.100.0/24), but hosts on each network must
communicate (as allowed by access lists). Without NAT, when a host on the inside network tries to access
a host on the overlapping DMZ network, the packet never makes it past the security appliance, which
sees the packet as having a destination address on the inside network. Moreover, if the destination
address is being used by another host on the inside network, that host receives the packet.
To solve this problem, use NAT to provide non-overlapping addresses. If you want to allow access in
both directions, use static NAT for both networks. If you only want to allow the inside interface to access
hosts on the DMZ, then you can use dynamic NAT for the inside addresses, and static NAT for the DMZ
addresses you want to access. This example shows static NAT.
To configure static NAT for these two interfaces, perform the following steps. The 10.1.1.0/24 network
on the DMZ is not translated.
Step 1 Translate 192.168.100.0/24 on the inside to 10.1.2.0 /24 when it accesses the DMZ by entering the
following command:
hostname(config)# static (inside,dmz) 10.1.2.0 192.168.100.0 netmask 255.255.255.0
Step 2 Translate the 192.168.100.0/24 network on the DMZ to 10.1.3.0/24 when it accesses the inside by
entering the following command:
hostname(config)# static (dmz,inside) 10.1.3.0 192.168.100.0 netmask 255.255.255.0
Step 3 Configure the following static routes so that traffic to the dmz network can be routed correctly by the
security appliance:
hostname(config)# route dmz 192.168.100.128 255.255.255.128 10.1.1.2 1
hostname(config)# route dmz 192.168.100.0 255.255.255.128 10.1.1.2 1
192.168.100.2
inside
192.168.100.0/24
outside
10.1.1.2
192.168.100.1
192.168.100.2
dmz
192.168.100.0/24
192.168.100.3
10.1.1.1
130029
192.168.100.3

 Loading...
Loading...