25-3
Cisco Security Appliance Command Line Configuration Guide
OL-10088-01
Chapter 25 Configuring Application Layer Protocol Inspection
Inspection Engine Overview
• State information for multimedia sessions that require inspection are not passed over the state link
for stateful failover. The exception is GTP, which is replicated over the state link.
• Some inspection engines do not support PAT, NAT, outside NAT, or NAT between same security
interfaces. See “Default Inspection Policy” for more information about NAT support.
Default Inspection Policy
By default, the configuration includes a policy that matches all default application inspection traffic and
applies inspection to the traffic on all interfaces (a global policy). Default application inspection traffic
includes traffic to the default ports for each protocol. You can only apply one global policy, so if you
want to alter the global policy, for example, to apply inspection to non-standard ports, or to add
inspections that are not enabled by default, you need to either edit the default policy or disable it and
apply a new one.
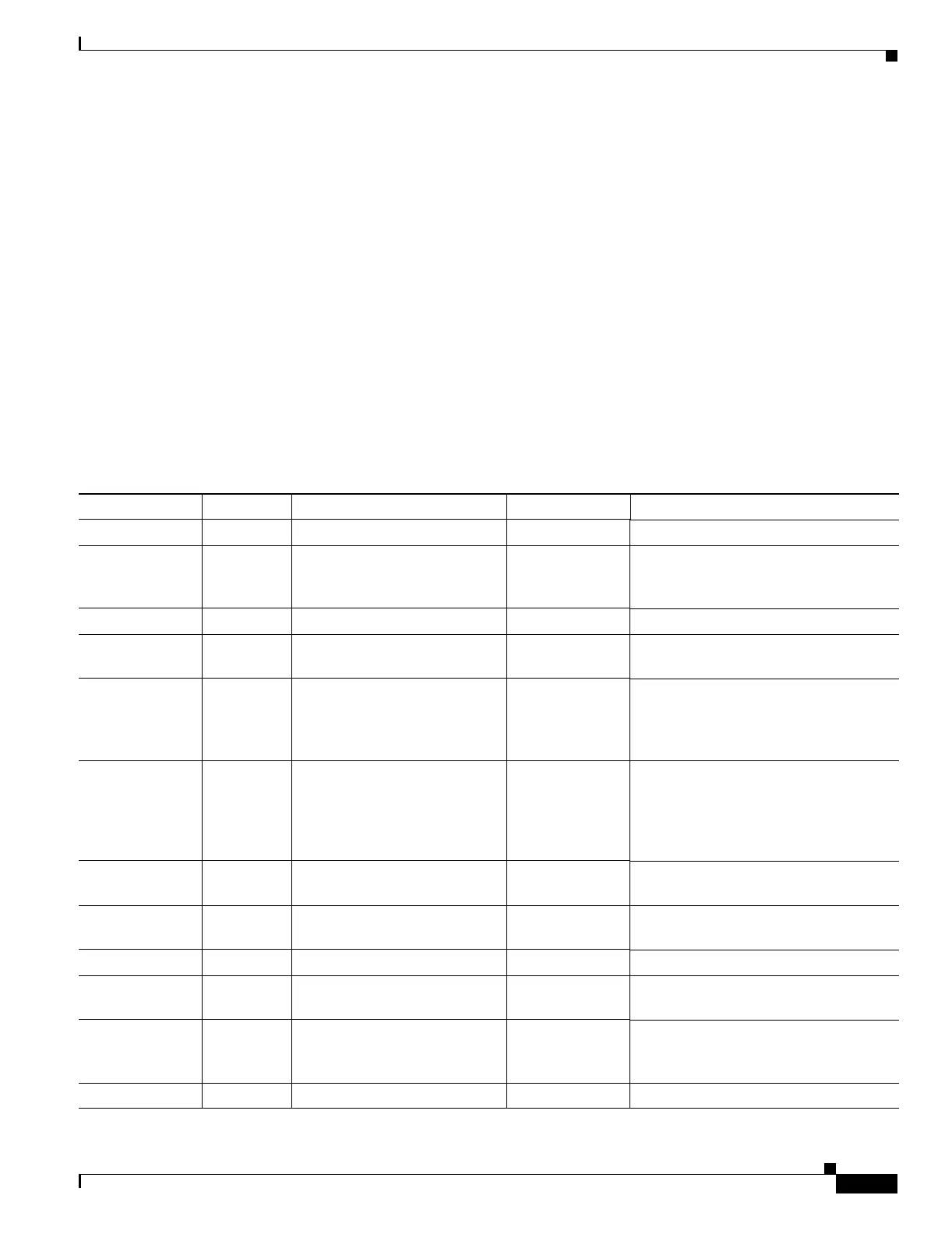
Table 25-1 lists all inspections supported, the default ports used in the default class map, and the
inspection engines that are on by default, shown in bold. This table also notes any NAT limitations.
Table 25-1 Supported Application Inspection Engines
Application
1
Default Port NAT Limitations Standards
2
Comments
CTIQBE TCP/2748 — ——
DNS over UDP UDP/53 No NAT support is available for
name resolution through
WINS.
RFC 1123 No PTR records are changed.
FTP TCP/21 — RFC 959 —
GTP UDP/3386
UDP/2123
— — Requires a special license.
H.323 H.225 and
RAS
TCP/1720
UDP/1718
UDP (RAS)
1718-1719
No NAT on same security
interfaces.
No static PAT.
ITU-T H.323,
H.245, H225.0,
Q.931, Q.932
—
HTTP TCP/80 — RFC 2616 Beware of MTU limitations stripping
ActiveX and Java. If the MTU is too
small to allow the Java or ActiveX tag to
be included in one packet, stripping
may not occur.
ICMP — — — All ICMP traffic is matched in the
default class map.
ICMP ERROR — — — All ICMP traffic is matched in the
default class map.
ILS (LDAP) TCP/389 No PAT. — —
MGCP UDP/2427,
2727
— RFC 2705bis-05 —
NetBIOS Name
Server over IP
UDP/137,
138 (Source
ports)
— — NetBIOS is supported by performing
NAT of the packets for NBNS UDP port
137 and NBDS UDP port 138.
PPTP TCP/1723 — RFC 2637 —
 Loading...
Loading...