431
SSL VPN configuration example
Network requirements
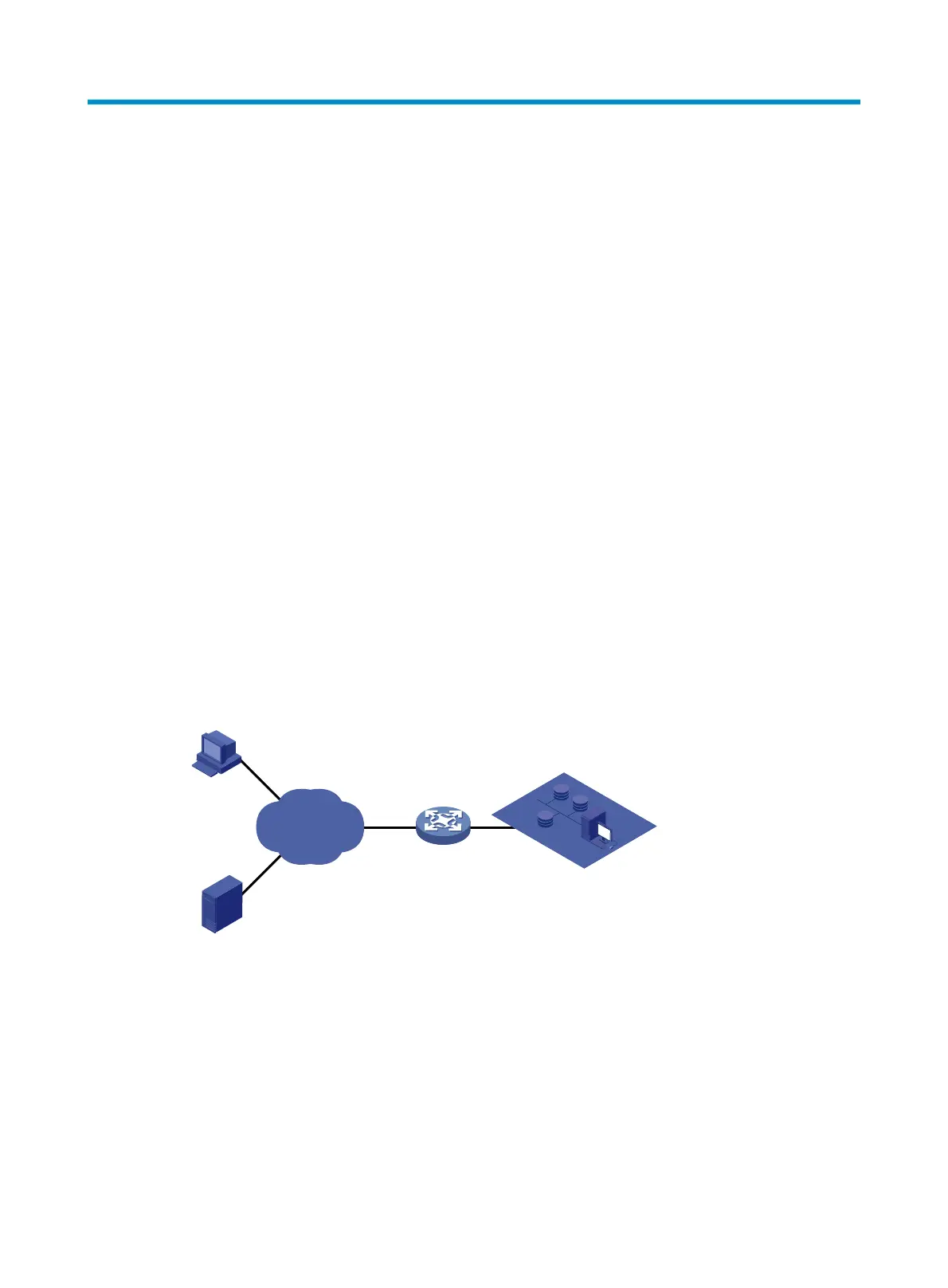
As shown in Figure 442, request a certificate and enable SSL VPN service on the SSL VPN gateway so
that users can use HTTPS to log in to the SSL VPN gateway to access the internal resources of the
corporate network.
In this configuration example:
• In this example, the CA runs the Windows Server and the SCEP plugin is required on the CA.
• The IP address of the SSL VPN gateway is 10.1.1.1/24. The IP address of the CA is 10.2.1.1/24, and
the name of the CA is CA server. The CA is used to issue certificates to the SSL VPN gateway and
remote users.
• Perform RADIUS authentication for SSL VPN users. The IP address of the RADIUS server (a IMC
server) is 10.153.10.131/24. After passing authentication, an SSL VPN user can access the internal
technology website whose IP address is 10.153.1.223, all hosts on subnet 10.153.2.0/24, and the
security sever whose IP address is 10.153.2.25 through the FTP shortcut.
• Configure a public account named usera. Specify that only one user can use the public account to
log in at a time. Configure local authentication for the public account and authorize a user who logs
in by using the public account to access the shared desktop provided by internal host
10.153.70.120.
• Specify the default authentication method as RADIUS for the SSL VPN domain and enable
verification code authentication.
Figure 442 Network diagram
Configuration prerequisites
• The SSL VPN gateway, the CA, and the hosts used by remote users can reach each other.
• The CA is enabled with the CA service and can issue certificates to the SSL VPN gateway and the
hosts.
• The RADIUS server is correctly configured to provide normal authentication function for users. In this
example, you need to configure the shared key as expert, configure the user account and user
group information, and add users to user group user_gr2.
Device
SSL VPN gateway
Host
Remote user
Internal servers
CA
Internet
10.2.1.1/24
10.1.1.1/24

 Loading...
Loading...