1-75
Cisco ASA Series CLI Configuration Guide
Chapter 1 Configuring Connection Profiles, Group Policies, and Users
Supporting a Zone Labs Integrity Server
Prerequisites
You have created Unified Access Rules with IPv6 addresses specified. If you have not created ACLs, see
Adding ACLs and ACEs, page 26-2.
Supporting a Zone Labs Integrity Server
This section introduces the Zone Labs Integrity server, also called the Check Point Integrity server, and
presents an example procedure for configuring the ASA to support the Zone Labs Integrity server. The
Integrity server is a central management station for configuring and enforcing security policies on
remote PCs. If a remote PC does not conform to the security policy dictated by the Integrity server, it is
not granted access to the private network protected by the Integrity server and ASA.
This section includes the following topics:
• Overview of the Integrity Server and ASA Interaction, page 70-76
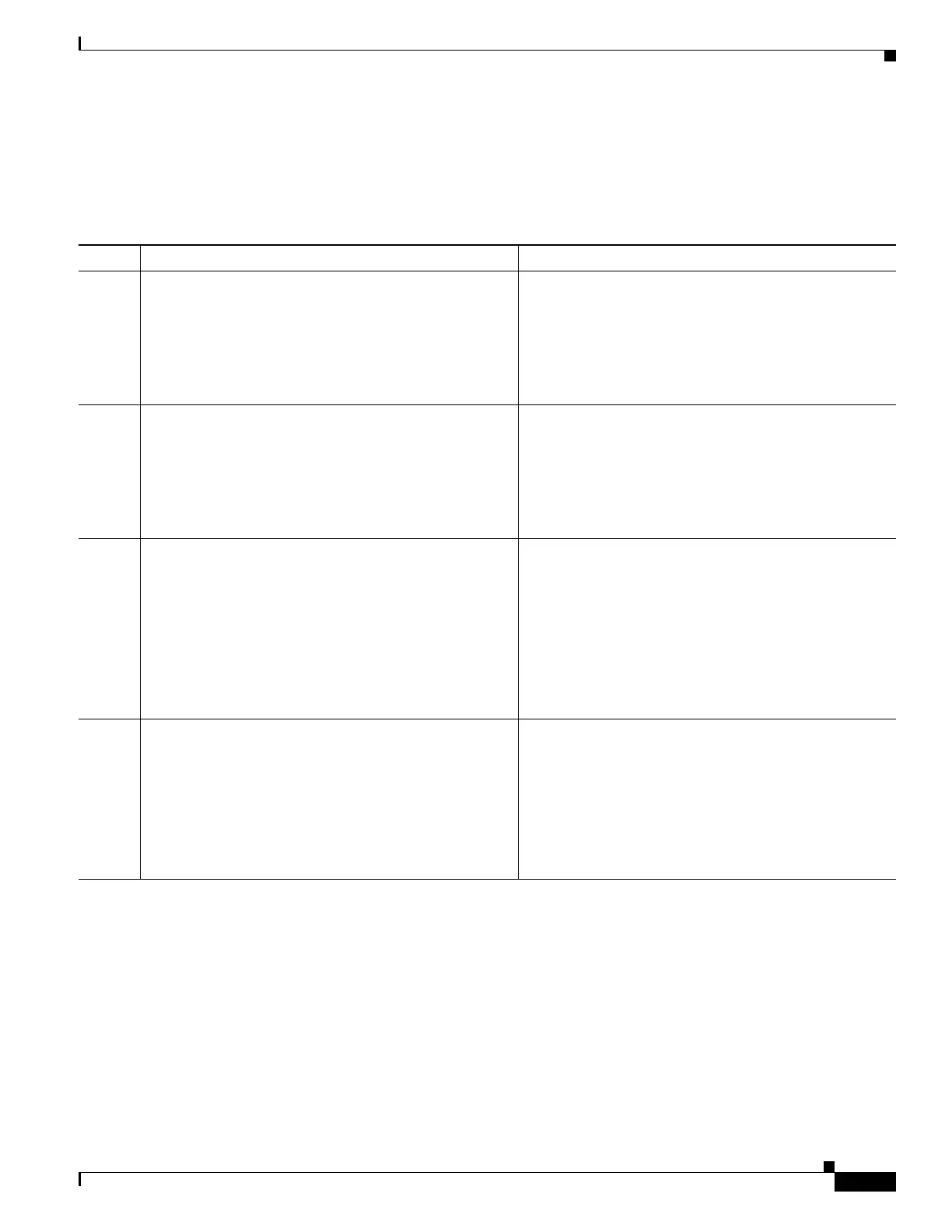
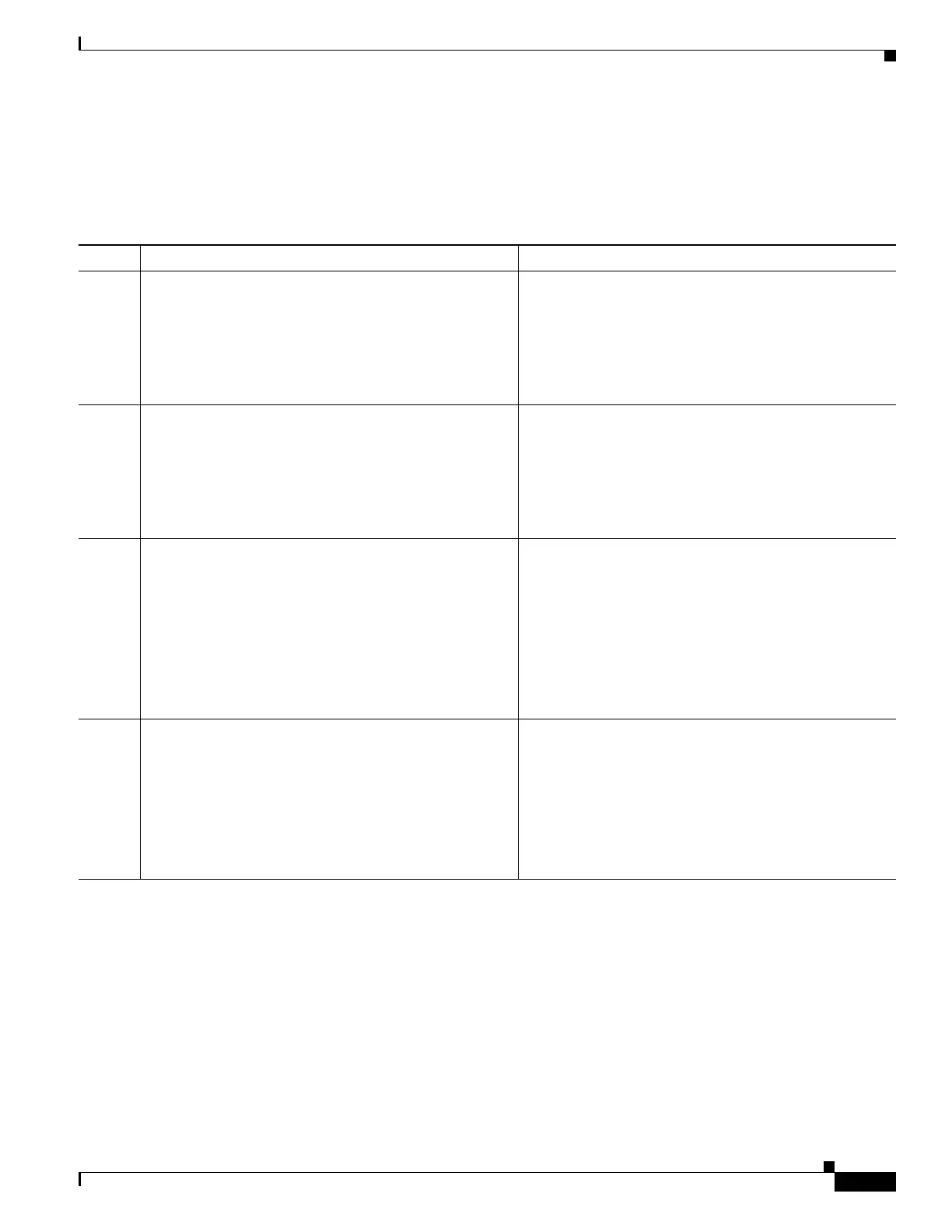
Tab le 1-1
Command Description
Step 1
webvpn
Example:
hostname(config)# group-policy ac-client-group
attributes
hostname(config-group-policy)# webvpn
hostname(config-group-webvpn)#
Enter webvpn group policy configuration mode.
Step 2
anyconnect firewall-rule client-interface
{private | public} value [RuleName]
Example:
hostname(config-group-webvpn)# anyconnect
fireall-rule client-iterface private value
ClientFWRule
Specifies an acces control rule for the private or public
network rule. The private network rule is the rule applied
to the VPN virtual dapter interface on the cient.
Step 3
show runn group-policy [value]
Example:
hostname(config-group-webvpn)# show runn
group-policy FirstGroup
group-policy FirstGroup internal
group-policy FirstGroup attributes
webvpn
anyconnect firewall-rule client-interface
private value ClientFWRule
Displays the group policy attributes as well as the
webvpn policy attribute for the group policy.
Step 4
(optional)
no anyconnect firewall-rule client-ineterface
private value [RuleName]
Example:
hostname(config-group-webvpn)#no anyconnect
firewall-rule client-ineterface private value
hostname(config-group-webvpn)#
Removes the client firewall rule from the private network
rule.
 Loading...
Loading...