1-4
Cisco ASA Series CLI Configuration Guide
Chapter 1 Configuring Management Access
Configuring ASA Access for ASDM, Telnet, or SSH
If you configure Telnet authentication (see the “Configuring Authentication for CLI and ASDM Access”
section on page 1-20), then enter the username and password defined by the AAA server or local
database.
Configuring SSH Access
To identify the client IP addresses and define a user allowed to connect to the ASA using SSH, perform
the following steps.
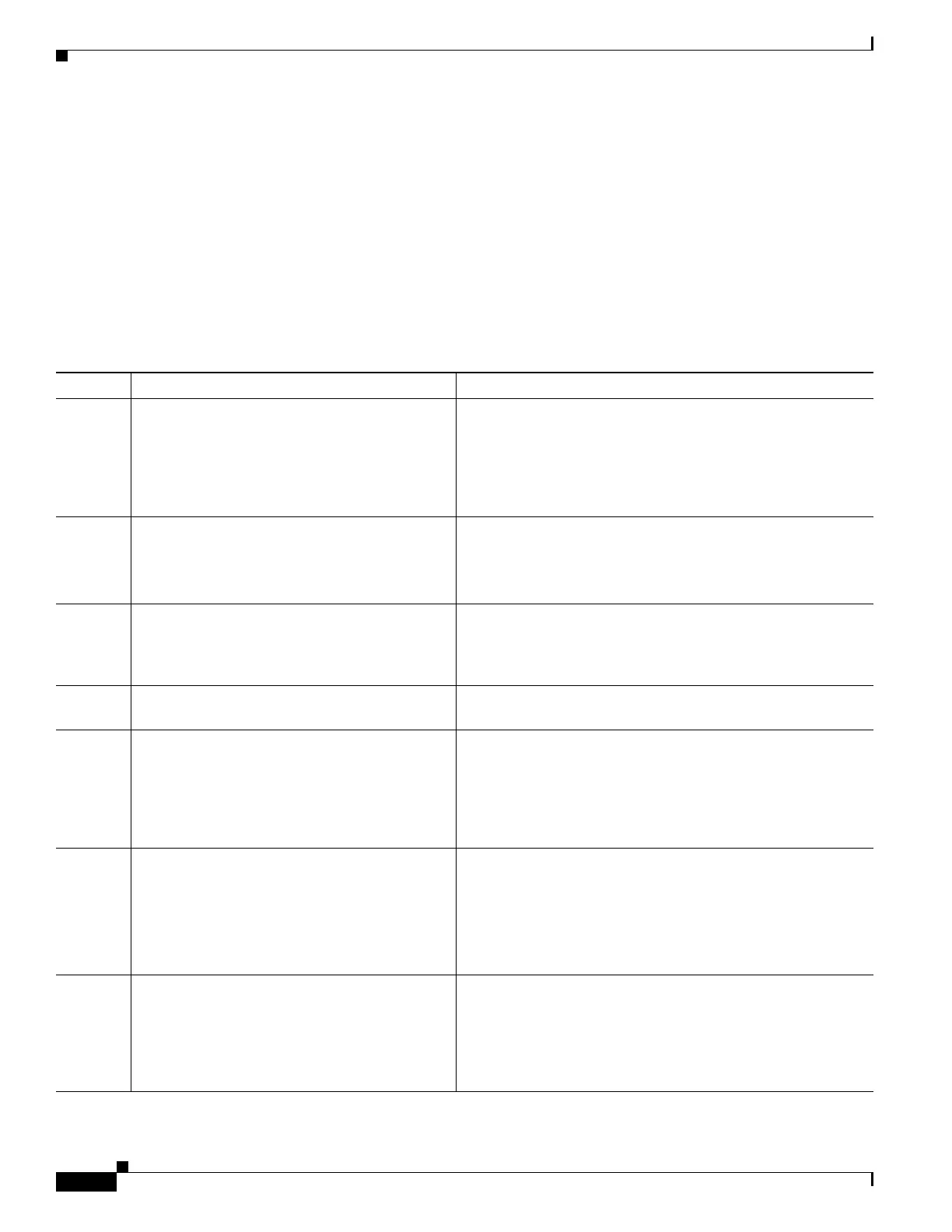
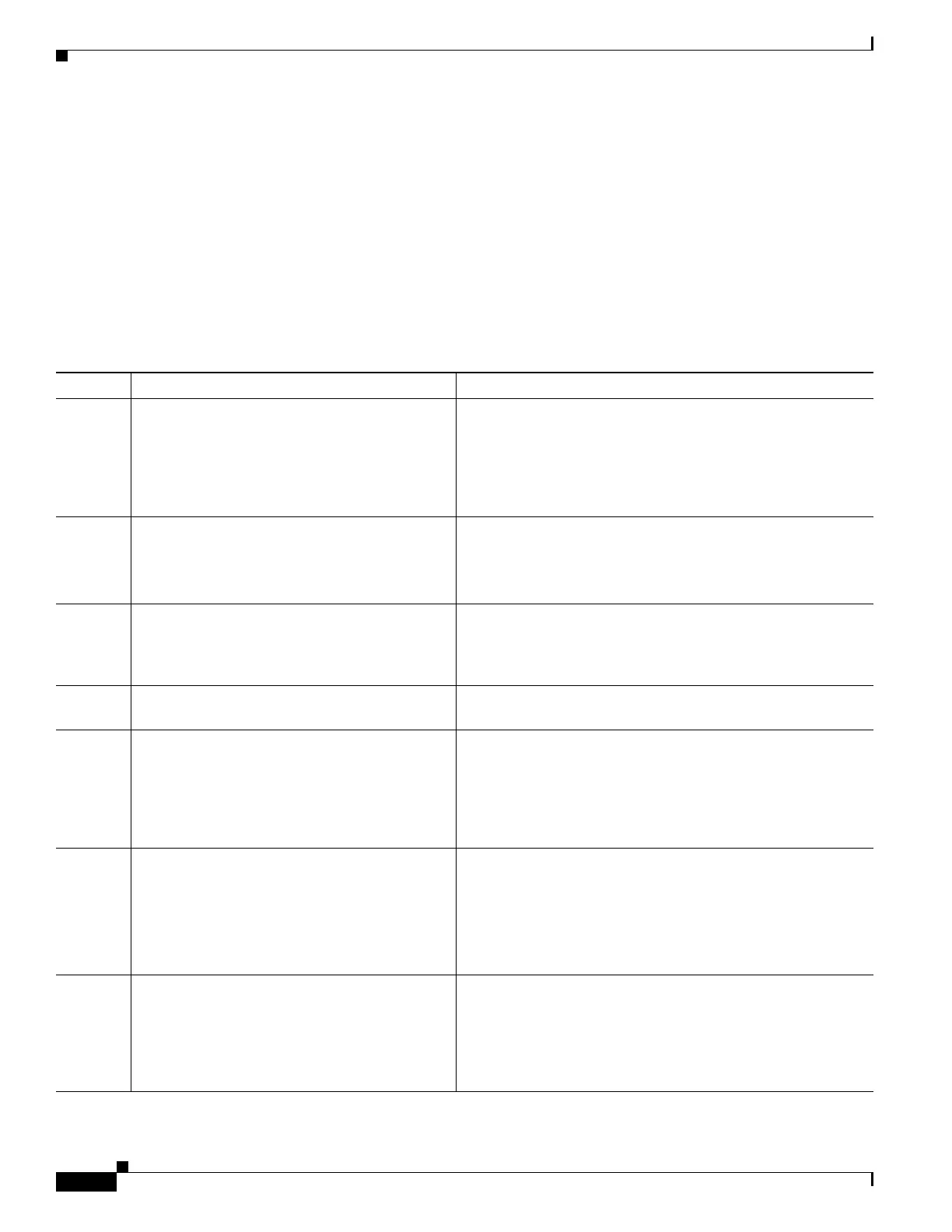
Detailed Steps
Command Purpose
Step 1
crypto key generate rsa modulus
modulus_size
Example:
hostname(config)# crypto key generate rsa
modulus 1024
Generates an RSA key pair, which is required for SSH.
The modulus value (in bits) is 512, 768, 1024, or 2048. The
larger the key modulus size you specify, the longer it takes to
generate an RSA key pair. We recommend a value of 1024.
Step 2
write memory
Example:
hostname(config)# write memory
Saves the RSA keys to persistent flash memory.
Step 3
aaa authentication ssh console LOCAL
Enables local authentication for SSH access. You can
alternatively configure authentication using a AAA server. See
the “Configuring Authentication for CLI and ASDM Access”
section on page 1-20 for more information.
Step 4
username username password password
Creates a user in the local database that can be used for SSH
access.
Step 5
ssh source_IP_address mask
source_interface
Example:
hostname(config)# ssh 192.168.3.0
255.255.255.0 inside
For each address or subnet, identifies the IP addresses from
which the ASA accepts connections, and the interface on which
you can SSH. Unlike Telnet, you can SSH on the lowest
security level interface.
Step 6
(Optional)
ssh timeout minutes
Example:
hostname(config)# ssh timeout 30
Sets the duration for how long an SSH session can be idle
before the ASA disconnects the session.
Set the timeout from 1 to 60 minutes. The default is 5 minutes.
The default duration is too short in most cases, and should be
increased until all pre-production testing and troubleshooting
have been completed.
Step 7
(Optional)
ssh version
version_number
Example:
hostname(config)# ssh version 2
Limits access to SSH version 1 or 2. By default, SSH allows
both versions 1 and 2.

 Loading...
Loading...