1-12
Cisco ASA Series CLI Configuration Guide
Chapter 1 Adding an Extended Access Control List
Where to Go Next
Where to Go Next
Many features use ACLs. Apply the ACL to an interface. See the “Configuring Access Rules” section
on page 1-7 for more information.
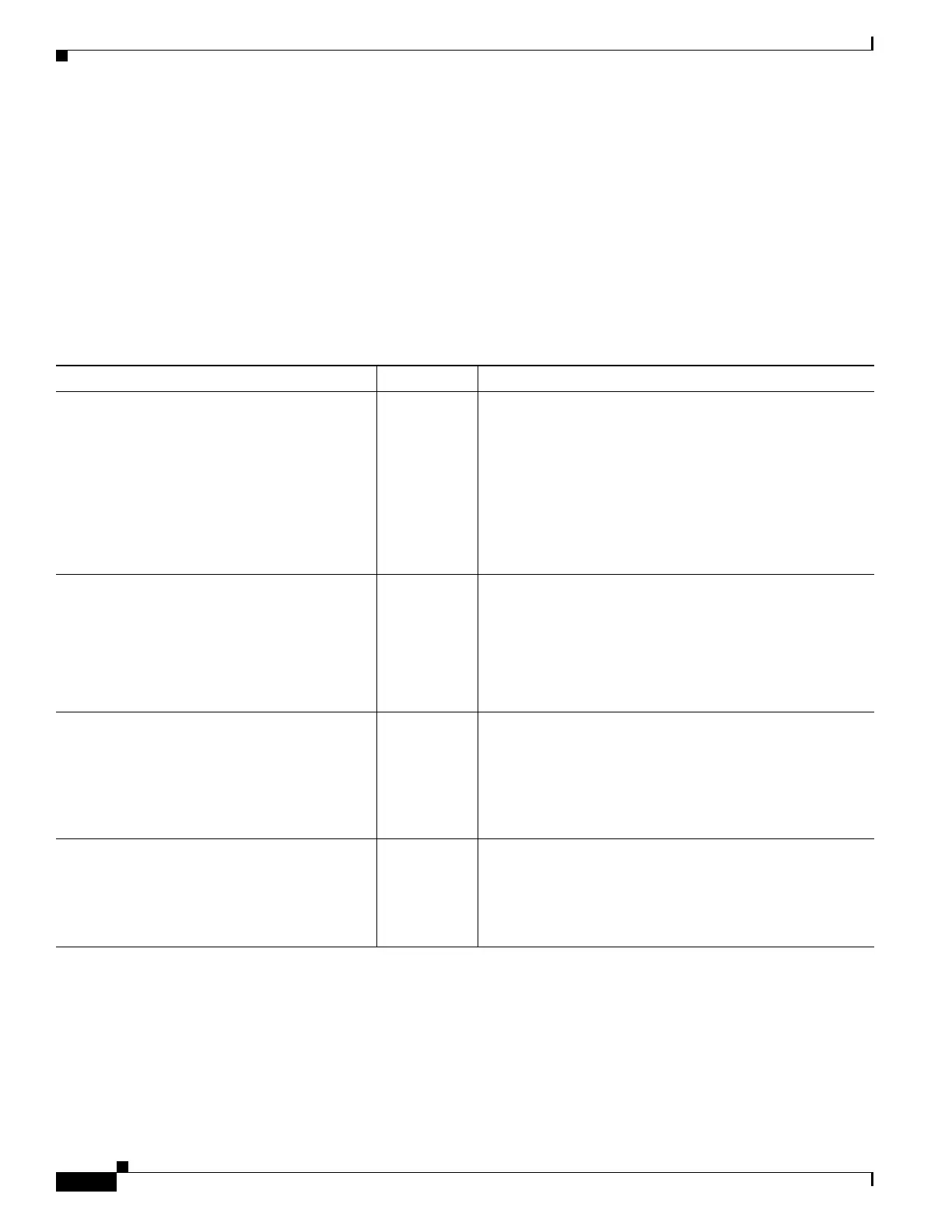
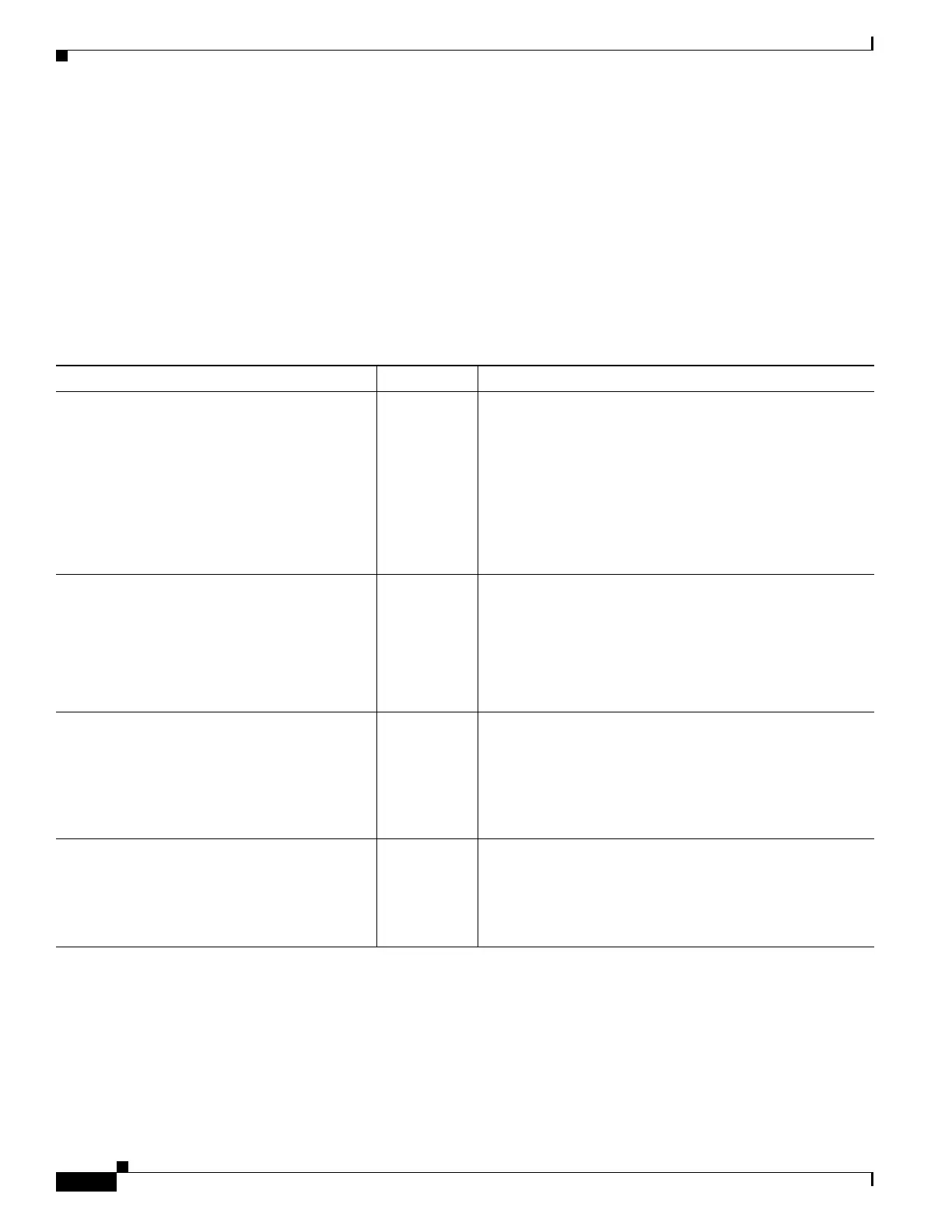
Feature History for Extended ACLs
Table 1-2 lists the release history for this feature.
Table 1-2 Feature History for Extended ACLs
Feature Name Releases Feature Information
Extended ACLs 7.0(1) ACLs are used to control network access or to specify traffic
for many features to act upon. An extended access control
list is made up of one or more access control entries (ACE)
in which you can specify the line number to insert the ACE,
the source and destination addresses, and, depending upon
the ACE type, the protocol, the ports (for TCP or UDP), or
the IPCMP type (for ICMP).
We introduced the following command: access-list
extended.
Real IP addresses 8.3(1) When using NAT or PAT, mapped addresses and ports are no
longer required in an ACL for several features. You should
now always use the real, untranslated addresses and ports
for these features. Using the real address and port means
that if the NAT configuration changes, you do not need to
change the ACLs. See the “Features That Use Real IP
Addresses” section on page 1-2 for more information.
Support for Identity Firewall 8.4(2) You can now use identity firewall users and groups for the
source and destination. You can use an identity firewall
ACL with access rules, AAA rules, and for VPN
authentication.
We modified the following commands: access-list
extended.
Support for TrustSec 9.0(1) You can now use TrustSec security groups for the source
and destination. You can use an identity firewall ACL with
access rules.
We modified the following commands: access-list
extended.

 Loading...
Loading...