Conguring the Network Security Settings
13WK-0AW
Authorized users may incur unanticipated losses from attacks by malicious third parties, such as sning, spoong,
and tampering of data as it ows over a network. To protect your important and valuable information from these
attacks, the machine supports the following features to enhance security and secrecy.
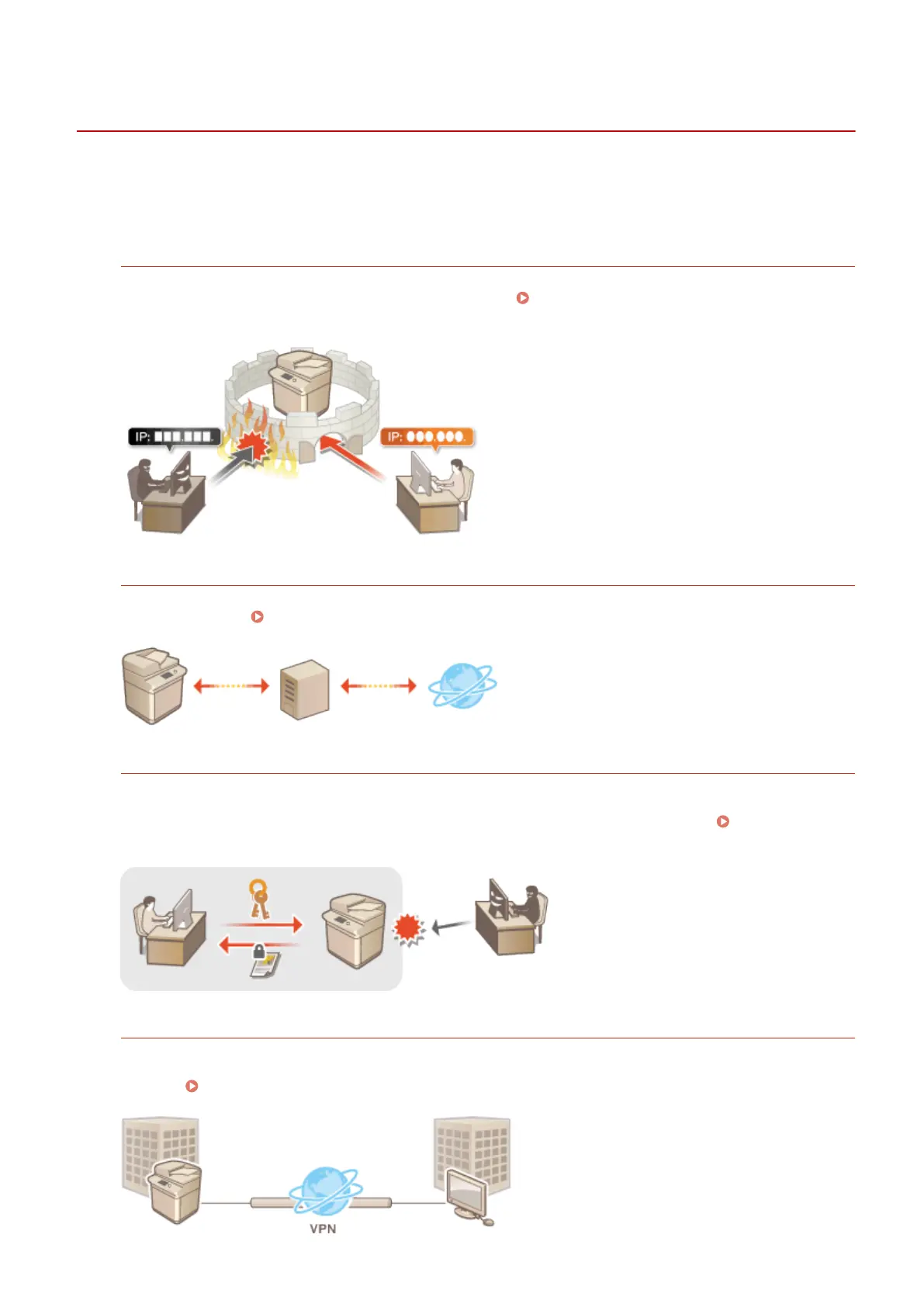
Firewall Settings
Unauthorized access by third parties, as well as network attacks and breaches, can be blocked by only allowing
communication with devices that have a specic IP address.
Restricting Communication by Using
Firewalls(P. 596)
Proxy Settings
You can provide greater security by using a proxy server for connections outside the network, such as when
browsing websites. Setting a Proxy(P. 602)
TLS Encrypted Communication
TLS is a protocol for encryption for data sent over a network and is often used for communication via a Web
browser or an e-mail application. TLS enables secure network communication when accessing the machine in a
variety of situations, such as when using the Remote UI or distributing device information. Conguring the
Key and Certicate for TLS(P. 604)
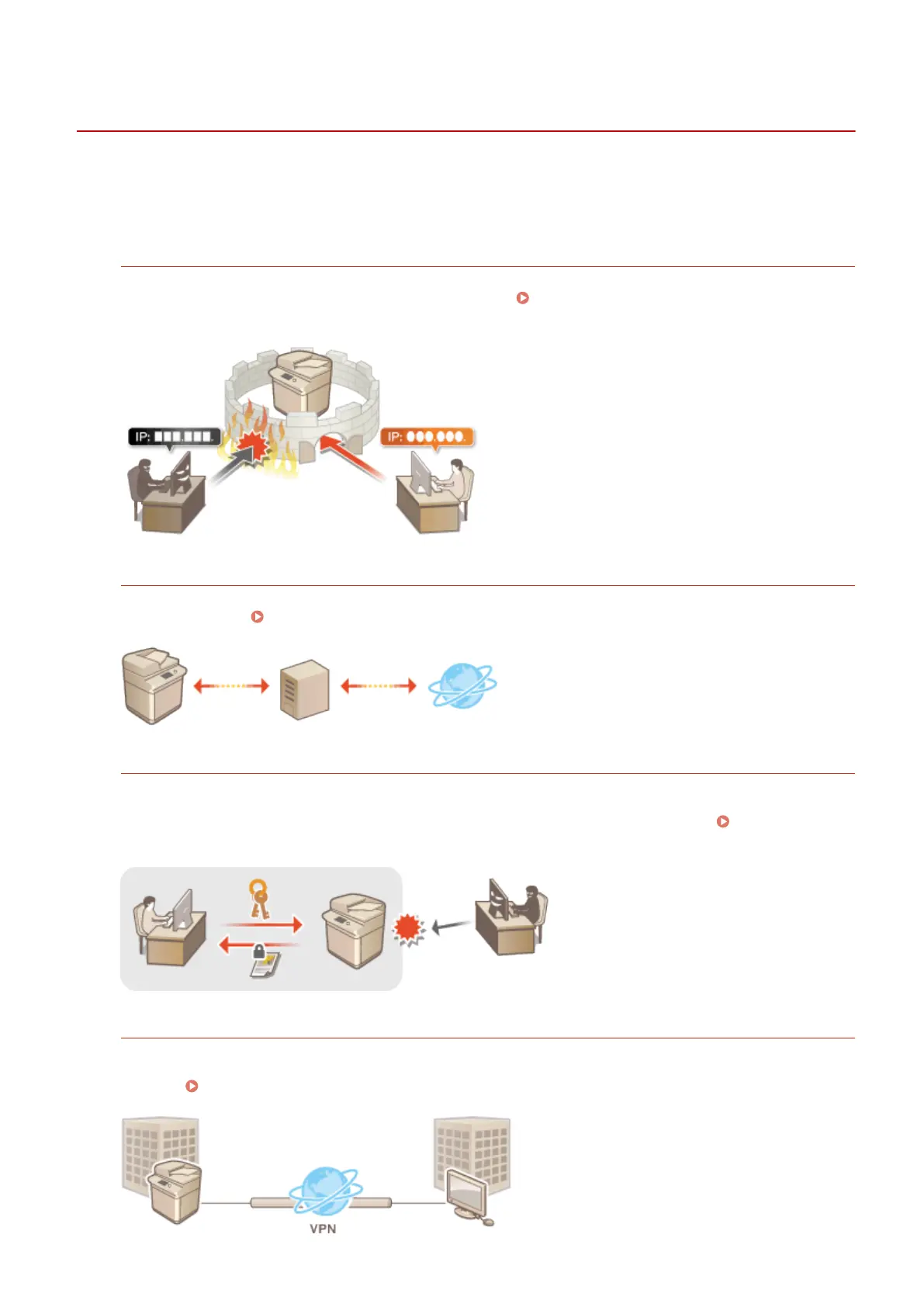
IPSec Communication
While TLS only encrypts data used on a specic application, such as a Web browser or an e-mail application,
IPSec encrypts the whole (or payloads of) IP packets. This enables IPSec to offer a more versatile security system
than TLS. Conguring the IPSec Settings(P. 608)
Managing the Machine
594

 Loading...
Loading...